Advanced Search
Content Type: Long Read
Following a series of FOI requests from Privacy International and other organisations, the Department of Health and Social Care has now released its contract with Amazon, regarding the use of NHS content by Alexa, Amazon’s virtual assistant. The content of the contract is to a big extent redacted, and we contest the Department of Health’s take on the notion of public interest.
Remember when in July this year the UK government announced a partnership with Amazon so that people would now…
Content Type: Advocacy
As any data protection lawyer and privacy activist will attest, there’s nothing like a well-designed and enforced data protection law to keep the totalitarian tendencies of modern Big Brother in check.
While the EU’s data protection rules aren’t perfect, they at least provide some limits over how far EU bodies, governments and corporations can go when they decide to spy on people.
This is something the bloc’s border control agency, Frontex, learned recently after coming up with a plan to…
Content Type: News & Analysis
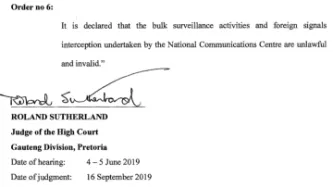
Today, the High Court of South Africa in Pretoria in a historic decision declared that bulk interception by the South African National Communications Centre is unlawful and invalid.
The judgment is a powerful rejection of years of secret and unchecked surveillance by South African authorities against millions of people - irrespective of whether they reside in South Africa.
The case was brought by two applicants, the amaBhungane Centre for Investigative Journalism and journalist Stephen…
Content Type: News & Analysis
The global counter-terrorism agenda is driven by a group of powerful governments and industry with a vested political and economic interest in pushing for security solutions that increasingly rely on surveillance technologies at the expenses of human rights.
To facilitate the adoption of these measures, a plethora of bodies, groups and networks of governments and other interested private stakeholders develop norms, standards and ‘good practices’ which often end up becoming hard national laws…
Content Type: Long Read
In December 2018, Privacy international exposed the dubious practices of some of the most popular apps in the world.Out of the 36 apps we tested, we found that 61% automatically transfer data to Facebook the moment a user opens the app. This happens whether the user has a Facebook account or not, and whether they are logged into Facebook or not. We also found that some of those apps routinely send Facebook incredibly detailed and sometimes sensitive personal data. Again, it didn’t matter if…
Content Type: News & Analysis
The Watson/Tele2 decision of the CJEU concerned section 1 and 2 of DRIPA and the Data Retention Regulations 2014. This contained the legislative scheme concerning the power of the Secretary of State to require communications service providers to retain communications data. Part 3 of the Counter-Terrorism and Security Act 2015 amended DRIPA so that an additional category of data - that necessary to resolve Internet Protocol addresses - could be included in a requirement to retain…
Content Type: Advocacy
RESPONSE OF PRIVACY INTERNATIONAL TO THE CONSULTATION ON THE GOVERNMENT’S PROPOSED RESPONSE TO THE RULING OF THE COURT OF JUSTICE OF THE EUROPEAN UNION ON 21 DECEMBER 2016 REGARDING THE RETENTION OF COMMUNICATIONS DATA
[Full response below]
Introduction
The consultation is in response to the judgment in Tele2 Sverige AB v Post-och telestyrelsen (Case-203/15) and R (Watson) v Secretary of State for the Home Department (Case C-698/15) [“Watson judgment”].
The case concerned…
Content Type: Long Read
Six years after NSA contractor Edward Snowden leaked documents providing details about how states' mass surveillance programmes function, two states – the UK and South Africa – publicly admit using bulk interception capabilities.Both governments have been conducting bulk interception of internet traffic by tapping undersea fibre optic cables landing in the UK and South Africa respectively in secret for years.Both admissions came during and as a result of legal proceedings brought by Privacy…
Content Type: Explainer
Recently the role of social media and search platforms in political campaigning and elections has come under scrutiny. Concerns range from the spread of disinformation, to profiling of users without their knowledge, to micro-targeting of users with tailored messages, to interference by foreign entities, and more. Significant attention has been paid to the transparency of political ads - what are companies doing to provide their users globally with meaningful transparency into how they…
Content Type: News & Analysis
While people may think that providing their photos and data is a small price to pay for the entertainment FaceApp offers, the app raises concerns about privacy, manipulation, and data exploitation—although these concerns are not necessarily unique to FaceApp.According to FaceApp's terms of use and privacy policy, people are giving FaceApp "a perpetual, irrevocable, nonexclusive, royalty-free, worldwide, fully-paid, transferable sub-licensable license" to use or publish the…
Content Type: News & Analysis
Today, Privacy International, along with nine other NGOs including Liberty and Amnesty International, attended a hearing before the Grand Chamber of the European Court of Human Rights (ECtHR) to revisit the Court's first ruling on our case challenging UK mass surveillance and intelligence sharing. In September 2018, the First Section of the ECtHR ruled that the UK government's mass interception program violates the rights to privacy and freedom of expression. Notwithstanding the positve aspects…
Content Type: Long Read
Join our campaign with Liberty and write to your local Police and Crime Commissioner (PCC). Your PCC works on your behalf to hold your local police force to account, so you can share your concerns about police spying tech with them.You can download our new campaign pack (pdf link at the bottom of the page) to learn more about the police surveillance technology that might already be being used in your local area, and find out what you can do to get your police force to be more accountable to you…
Content Type: Long Read
IMAGE SOURCE: "My Phone Bought This" by oliver t is licensed under CC BY-NC-ND 4.0.
LAST UPDATE: 16th May 2022.
Mandatory SIM card registration laws require people to provide personal information, including a valid ID or even their biometrics, as a condition for purchasing or activating a SIM card. Such a requirement allows the state to identify the owner of a SIM card and infer who is most likely making a call or sending a message at any given time.
SIM card…
Content Type: Long Read
When you go abroad, you expect to show your passport right? But what if immigration authorities wanted access to your Facebook, Instagram and Twitter accounts before they let you enter a country? What if they wanted to vet you based on your updates, photos, likes, retweets and even your DMs?We think social media companies, who make literally billions of dollars out of you, and wield massive power and influence, should challenge governments on YOUR behalf. They should be protecting their users…
Content Type: Case Study
In 2030 Amtis finds a future where property rights for data were adopted. Here’s how this future plays out:
My data, my turf. This was the first graffiti I saw as I was walking down the street and I said to myself, “Yeah, big corp, we’re going to get you good!”. I am fed up with companies making insane amounts of money from my data. If this is the game we’re playing, I want my fair share.
I was not the only one thinking like this. A few years back there was a strong push towards adopting…
Content Type: Video
Watch our video primer (1m54s) on how political advertisers use highly detailed data about you to target political adverts at you.
Read about some simple steps you can take to minimise the amount of political ads you see online and questions you can be asking of those that profit from your data.
Content Type: Long Read
Details of case:
R (on the application of Privacy International) (Appellant) v Investigatory Powers Tribunal and others (Respondents)
[2019] UKSC 22
15 May 2019
The judgment
What two questions was the Supreme Court asked to answer?
Whether section 67(8) of RIPA 2000 “ousts” the supervisory jurisdiction of the High Court to quash a judgment of the Investigatory Powers Tribunal for error of law?
Whether, and, if so, in accordance with what principles, Parliament may by…
Content Type: Press release
The Irish Data Protection Commission has today launched an inquiry into the data practices of ad-tech company Quantcast, a major player in the online tracking industry. PI's 2018 investigation and subsequent submission to the Irish DPC showed how the company is systematically collecting and exploiting people's data in ways people are unaware of. PI also investigated and complained about Acxiom, Criteo, Experian, Equifax, Oracle, and Tapad.
PI welcomes this announcement and its focus on…
Content Type: Long Read
Last week, an investigation by Bloomberg revealed that thousands of Amazon employees around the world are listening in on Amazon Echo users.
As we have been explaining across media, we believe that by using default settings and vague privacy policies which allow Amazon employees to listen in on the recordings of users’ interactions with their devices, Amazon risks deliberately deceiving its customers.
Amazon has so far been dismissive, arguing that people had the options to opt out from the…
Content Type: Video
Video courtesy of CPDP (https://www.cpdpconferences.org/)
What is the impact of online gender-based violence on survivors? What should be the role of companies in fighting this phenomenon? What is the link between the right to privacy? In this panel, which took place at CPDP in February 2019, academics, civil society and government representatives discuss the issue of online gender based violence with a privacy lens.
Chair: Gloria González Fuster, VUB -LSTS (BE)
Moderator: Valerie…
Content Type: News & Analysis
In December 2018, we revealed how some of the most widely used apps in the Google Play Store automatically send personal data to Facebook the moment they are launched. That happens even if you don't have a Facebook account or are logged out of the Facebook platform (watch our talk at the Chaos Communication Congress (CCC) in Leipzig or read our full legal analysis here).Today, we have some good news for you: we retested all the apps from our report and it seems as if we…
Content Type: News & Analysis
Palantir and the UN’s World Food Programme (WFP) are partnering for a reported $45 million. Palantir, a US-based company that sells data software and has been the centre of numerous scandals.
The World Food Programme provides assistance in food and nutrition to around 92 million people each year. Systems that are produced in agreements such as the one between WFP and Palantir increase risks to the people the they are attempting to help. There are risks to both individuals and whole populations…
Content Type: Press release
FOR IMMEDIATE RELEASE
December 21, 2018
CONTACTS:
Alex Betschen, Civil Liberties & Transparency Clinic, [email protected], 716–531–6649
Colton Kells, Civil Liberties & Transparency Clinic, [email protected], 585–766–5119
Abdullah Hasan, ACLU, [email protected], 646–905–8879
NEW YORK — Privacy International, the American Civil Liberties Union, and the Civil Liberties & Transparency Clinic of the University at Buffalo School of Law filed a lawsuit today…
Content Type: Impact Case Study
What HappenedOn 5 June 2013, The Guardian published the first in a series of documents disclosed by Edward Snowden, a whistleblower who had worked with the NSA. The documents revealed wide-ranging mass surveillance programs conducted by the USA’s National Security Agency (NSA) and the UK’s Government Communications Headquarters (GCHQ), which capture the communications and data of hundreds of millions of people around the world. In addition to revealing the mass surveillance programs of the NSA…
Content Type: Long Read
Yesterday, the European Court of Human Rights issued its judgement in Big Brother Watch & Others V. the UK. Below, we answer some of the main questions relating to the case.
What's the ruling all about?
In a nutshell, one of the world's most important courts, the European Court of Human Rights, yesterday found that certain UK laws about how intelligence agencies can spy on our internet communications breach our human rights. These surveillance laws have meant that the UK intelligence…
Content Type: News & Analysis
Around the world, from North America to Europe and Asia, governments are starting to roll out smart meters. While the technology promises increased energy efficiency through greater consumer control over energy consumption, smart meters also raise serious privacy concerns. Smart meters collect energy usage data at high frequencies - typically every five, fifteen or 30 minutes. That level of granularity reveals how much electricity is being used in a home and when, which in turn can paint an…
Content Type: News & Analysis
Our intervention comes on the back of mounting evidence that the South African state’s surveillance powers have been abused, and so-called “checks & balances” in RICA have failed to protect citizens’ constitutional right to privacy.
Among our core arguments are:
That people have a right to be notified when their communications have been intercepted so that they can take action when they believe their privacy has been unlawfully breached. Currently RICA prevents such notification, unlike…
Content Type: News & Analysis
Photo was found here
This essay was published in The Sur International Journal of Human Rights, Issue 27, July 2018.
Abstract:
This essay focuses on elections in Kenya and analyses the use of technology and the exploitation of personal data in both the electoral process and campaigning. We only need to look to Kenya’s election history to understand why it is important. The 2007/2008 election resulted in violence that killed over 1,000 people and displaced over 600,000. The 2013 election was…
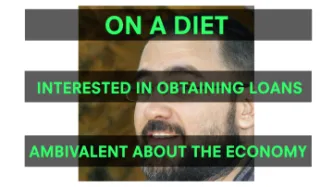
Content Type: Press release
On the day that GDPR comes into force, PI has launched a campaign investigating a range of data companies that make up a largely hidden data ecosystem. This hidden data ecosystem is comprised of thousands of non-consumer facing data companies - such as Acxiom, Criteo, Quantcast - that amass and exploit large amounts of personal data. Using the rights and obligations provided for within the new data privacy law, PI's campaign involves investigating a selection of these companies whose business…