Where is our encrypted cloud?
In the PI office, we have daily debates about which platforms to use for our organizational operations. As a privacy charity, we are naturally concerned about the integrity of our own information services and resources, but we frequently receive queries about the best technologies to use from a variety of other organizations, some with very complex threat models.
The sad fact is that we are all poorly served by the range of services currently available. We worry that there is a significant lack of outsourced/cloud-mediated services that include effective content privacy protections. If you know of resources that are out there or under development, please get in touch or leave a comment below.
Plugging-in cryptography
At the moment, we're talking about cryptography services on general-use devices. Of course, cryptophones are a great idea and we're excited about some recent developments in that arena, but what we really need are cryptography-enabled add-ons to services that we all use: calendaring and document collaboration being the obvious two, with trusted and transparent plug-ins as well.
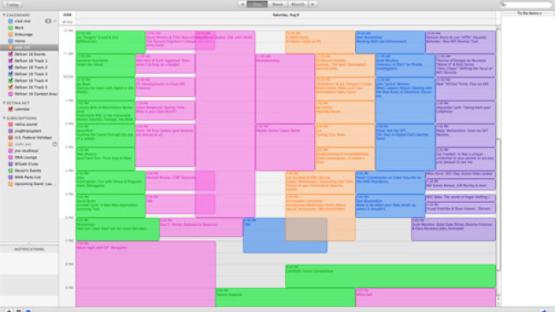
If you want to use email to communicate securely within your organisation or with external parties, you don't need to use a specialised service provider or specialised device - you can simply use cryptography at the top layer, for example, with a plug-in to your email client that allows PGP. But where is the equivalent for calendaring? Currently available calendaring services allow providers access to information about who you're meeting, when you're meeting with them and what you're meeting about. A general user might be unconcerned, but professionals should be very worried about the privacy of their business engagements - access to the calendars of corporate executives could identify all of a company's clients, and potentially any impending mergers and acquisitions. Similarly, the calendars of human rights defenders and journalists could put their colleagues and sources in danger.
We're not aware of any plug-ins that allow the use of normal calendar syncing services while encrypting the content. Of course, even if cryptography was used it would still allow the cloud services provider to see when you're busy and when you're not, but at least those services would be unable to see what you're actually doing.
We would also love to see a tool that enables encryption of collaboratively-edited rich text documents. Everything seems to be heading to the cloud, now that both Apple and Microsoft have implemented a 'take it or leave it' approach to storing professional files in the cloud for sharing and collaboration and Google Docs is increasingly the go-to alternative. We are certainly fond of Etherpad, but ideally we would be able to run it on a remote server (perhaps in a more reliable jurisdiction) and enable encryption. Couldn't a browser plug-in be designed that would allow the content of the documents to be encrypted within the browser? The key management would undoubtedly be complex and the processing burdens would be significant, but a Google Docs-style editing environment with data protected against the server would be a great asset for hundreds of organizations around the world.
Designing in privacy and security
This is only the start of our quest - real security and privacy requires much more than just content encryption. In the case of email, only the content of a message may be protected, but the email service provider would still know who you are emailing and who is emailing you, and can be compelled to hand over that information to law enforcement. Nonetheless, the use of encrypted email is a step up in security with minimal pain (provided the plug-ins are secure).
We need to get smarter about our cloud services. Governments want the same levels of access to our cloud transactions as they have to our phone records. Why does this matter? In the old days, we kept files on our computer, and we emailed them around, and everything was fine. We used internal networks that we ran ourselves. If malicious people or law enforcement officers wanted your files they would have to gain access to your computer or your network. Sometimes they would have to knock on your door and ask nicely. If we let governments treat cloud services like telcos, they will be able to demand the identities of everyone working on a specific document, as well as access to that document, from the cloud service provider. Most importantly, the subjects of the requests for information would never know they'd been targeted - the cloud provider would probably be barred from notifying them.
The first step to fixing this problem is to build encryption into the cloud services. This is relatively easy compared to solving the second problem: finding a way to protect the information about the files.
Until these services can be made more secure, we face a nasty trade-off between access, security and usability. We can only hope that smarter people than us are thinking about these problems.