Remembering surveillance of the past informs privacy fights today
In the late eighteenth century in Germany, ‘anthropologist’ Johann Blumenbach published a degenerative hypothesis that linked cranium and facial profiles to supposed character traits and accordingly divided human beings into five different races: the Caucasian, Mongolian, Malayan, Ethiopian, and American.1
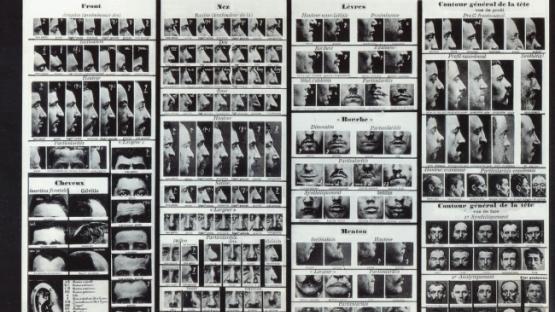
In the 1870s, Alphonse Bertillon, a police officer in France, started a trend to identify criminals based on facial characteristics, alongside subsequent use of the camera to photograph and identify repeat offenders.
In the 1930s in Nazi Germany, IBM computer scientists devised an identification system in aid of the Third Reich’s attempt to systematically decimate entire populations.2
Governments—in coordination with the private sector—continue to improve their ability to collect data on, catalogue, and surveil people. The advancement in technology has coincided with if not been driven by an increasing need for states to control ever-growing populations. Fingerprinting, retinal scans, facial recognition, among other forms of documentation and identification are more recent incarnations. With each technological advance, albeit positive in many respects, comes an opportunity to document, criminalize, incarcerate, and perhaps terminate.
As racism and sexism are defining elements of our time, improvement of surveillance technology will continue to enable abuse.
Documenting people during the days of empire was a main method of control employed by colonial nations. Predicated upon an obsession to maintain racial purity, authorities enacted legislation and document identification programs in efforts to mandate separation, or at least regulate, interaction between native and colonist, in a number of African and Asian colonies.3 People within these colonies were taxonomically categorised and classified, both to monitor any activity that would challenge colonial rule, but also implicitly to ‘scientifically’ establish white European superiority and maintain separation between ‘ruled’ and ‘ruler’.
Often, this sort of regulatory surveillance implicated the intimate. One of the earliest instances of widespread use of identification cards were for the purpose to identify and regulate women who were suspected or considered to be a prostitute.4 Venereal disease and its extremely damaging impact on the male soldier and labourer population were a major concern of colonial governments. Women—believed to be the primary ‘carriers’ of these diseases—were to be ‘managed’ hygienically in what are today Hong Kong Special Administration Region of China, India, Indonesia, Malaysia, Singapore, and Viet Nam, among others.
Regulated systems of subjugation and at times imprisonment of women in colonies tended to be violent and oppressive. Those involved in this work were required to possess ‘prostitute’ identification cards that identified their race, whether they had been to hospital, and if they were ‘infected.’ They were forced by law to obey mandatory check-up schedules and go to lock hospitals if they were found to be sick. Women who were arrested or came of their own volition for treatment were then forced to remain until properly ‘treated’ for venereal disease, which we now know was ineffective medically and generally extremely painful.5
Intrusive state surveillance techniques are not an exception but the rule of Anglo-European history. This is just one example of a governing power’s documentation and surveillance of types of people in efforts to control a population. These technologies have been incorporated into policing and penal methods back in the coloniser’s state. Today, assisted with the efficacy and speed of the internet, data collection and monitoring of people has proven highly effective for governments around the world to maintain a tight grip over populations, and for companies to better target individuals in advertising.
In many industrializing countries, the leftover architecture of colonial control—huge databases and identity documentation schemes for example—can be useful in delivering aid or for state centralization efforts, but can also be used as a tool to subjugate. Telecoms may be flocking to Southeast Asia and Sub-Saharan Africa—to name two areas—connecting people at lightning rates, yet this coincides with generally no regulation or implementation of data and privacy protection. Government surveillance capabilities are now global.
The more we give information on ourselves, to both the government and to the private sector, we have to question whether this corresponds with our expectations of privacy - in the broadest sense of the word. Yet, a global free market approach to data collection is untenable. Private digital enclosure is already occurring and the internet is certainly not free. Regulation—both domestic and international—is one point of resistance to tip the balance of power slightly in people’s favour. Globally improving knowledge on online privacy safety is another.
We need to continue to flesh out the close relationship between data collection, surveillance, and use and abuse of power, see the unprecedented nature of what we continue to learn from events such as the Snowden revelations, and underscore the need to understand, and when necessary, regulate, this ever-growing machine of public and private data collection. Remembering the past can help to remind us all to stay vigilant in the present and future.