Advanced Search
Content Type: Long Read
Yesterday, the European Court of Human Rights issued its judgement in Big Brother Watch & Others V. the UK. Below, we answer some of the main questions relating to the case.
What's the ruling all about?
In a nutshell, one of the world's most important courts, the European Court of Human Rights, yesterday found that certain UK laws about how intelligence agencies can spy on our internet communications breach our human rights. These surveillance laws have meant that the UK intelligence…
Content Type: News & Analysis
Around the world, from North America to Europe and Asia, governments are starting to roll out smart meters. While the technology promises increased energy efficiency through greater consumer control over energy consumption, smart meters also raise serious privacy concerns. Smart meters collect energy usage data at high frequencies - typically every five, fifteen or 30 minutes. That level of granularity reveals how much electricity is being used in a home and when, which in turn can paint an…
Content Type: News & Analysis
Our intervention comes on the back of mounting evidence that the South African state’s surveillance powers have been abused, and so-called “checks & balances” in RICA have failed to protect citizens’ constitutional right to privacy.
Among our core arguments are:
That people have a right to be notified when their communications have been intercepted so that they can take action when they believe their privacy has been unlawfully breached. Currently RICA prevents such notification, unlike…
Content Type: News & Analysis
Photo was found here
This essay was published in The Sur International Journal of Human Rights, Issue 27, July 2018.
Abstract:
This essay focuses on elections in Kenya and analyses the use of technology and the exploitation of personal data in both the electoral process and campaigning. We only need to look to Kenya’s election history to understand why it is important. The 2007/2008 election resulted in violence that killed over 1,000 people and displaced over 600,000. The 2013 election was…
Content Type: Press release
On the day that GDPR comes into force, PI has launched a campaign investigating a range of data companies that make up a largely hidden data ecosystem. This hidden data ecosystem is comprised of thousands of non-consumer facing data companies - such as Acxiom, Criteo, Quantcast - that amass and exploit large amounts of personal data. Using the rights and obligations provided for within the new data privacy law, PI's campaign involves investigating a selection of these companies whose business…
Content Type: Impact Case Study
PI and our global partners have been at the forefront of challenging communications data retention for over a decade.
What is the problem
Communications data, also known as metadata, tells a story about your digital activity and answers the who, when, what, and how of a specific communication. While communications data doesn't include the contents of a message, all of the other information about the message can be very revealing about people, their habits, thoughts, health and personal…
Content Type: Impact Case Study
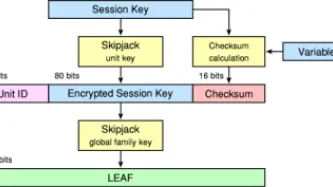
What happenedThe Clinton Administration kicked off the cypto-wars in 1993 with the Clipper Chip. The continued application of export controls restrained the deployment of strong cryptography in products at a key moment of internet history: as it began to be embedded in software and networking. What we didIn the early phases of the crypto-wars we placed pressure on global industry to implement encryption in their products. We ran campaigns and events across the world on the need for strong…
Content Type: Impact Case Study
What is the problem
For over two decades we have been documenting an alarming use and spread of surveillance. It is no longer just the wars on terror or drugs or migration that is driving this trend. The management of health crises and distribution of welfare regularly are among others being used to justify this turn to increasingly invasive forms of surveillance. From country to country we see the same ideas and the same profiteers expanding their reach.
When we first released our report on…
Content Type: Impact Case Study
What is the problem
Business models of lots of companies is based on data exploitation. Big Tech companies such Google, Amazon, Facebook; data brokers; online services; apps and many others collect, use and share huge amounts of data about us, frequently without our explicit consent of knowledge. Using implicit attributes of low-cost devices, their ‘free’ services or apps and other sources, they create unmatched tracking and targeting capabilities which are being used against us.
Why it is…
Content Type: Impact Case Study
What happenedIn the aftermath of 9/11, Governments across the world rushed to legislate to expand surveillance. GovernmentsMoved to limit debate and reduce consultations as they legislated with speed.Created new systems to collect data on all travellers, for the purpose of profiling and risk scoring.Expanded identity schemes, and began demanding biometrics, particularly at borders.Developed financial surveillance mechanisms on an unprecedented scale.What we didFew non-governmental…
Content Type: Impact Case Study
What happenedGovernments continuously seek to expand their communications surveillance powers. In the 1990s it was in the context of applying telephone surveillance laws to the internet. In the 2000s a spate of new laws arrived in response to 9/11. Expansions were then sought to monitor over-the-top services within the framing of Web 2.0. Then in the post-Snowden environment Governments rushed to legislate their previously secret powers.What we didWe supported…
Content Type: Impact Case Study
What is the problem
In the 1990s privacy was often maligned as a ‘rich Westerner’s right’. We were told often that non-Westerners didn’t need privacy and had different cultural attitudes and would greet surveillance policies and technologies — often exported from the West.
Global civil society was composed mostly of a few individuals with no resources but great passion. The larger and more established NGOs, such as consumer and human rights organisations were less interested in ‘digital’ and ‘…
Content Type: Impact Case Study
What happenedSince the late 1980s governments across the world have been trying to build identity registries. By the early 1990s, there were similar policies being pursued by a number of governments across the Pacific region, with similar technologies from the same companies. In the mid-90s ID cards became a ‘modern’ policy, implementing smart cards. By 9/11 biometric IDs became the preferred solution to undefinable problems. Then came vast databases of biometrics to identify people — with…
Content Type: Impact Case Study
[Photo By Ludovic Courtès - Own work, CC BY-SA 3.0] Last update: 14 December 2022What is the problem and why it is importantUntil the early '10s, the right to privacy had been sidelined and largely unaddressed within the UN human rights monitoring mechanisms, despite being upheld as a fundamental human right in the Universal Declaration of Human Rights and the International Covenant on Civil and Political Rights (ICCPR).Beyond the ICCPR General Comment No.16: Article 17 (…
Content Type: Impact Case Study
What happenedStrong and effective data protection law is a necessary safeguard against industry and governments' quest to exploit our data. A once-in-a-generation moment arose to reform the global standard on data protection law when the European Union decided to create a new legal regime. PI had to fight to ensure it wasn't a moment where governments and industry would collude to reduce protections.In January 2012, the European Commission published a proposal to comprehensively reform the…
Content Type: Long Read
TO TAKE PART IN OUR CAMPAIGN, RIGHT CLICK ON THE PICTURES BELOW, SAVE THEM, AND SHARE THEM ON SOCIAL MEDIA TAGGED #SPYPOLICE
Have you ever been to a peaceful protest, demo or march? Did you assume that the police would only be identifying 'troublemakers'? How would you feel if just by turning up at a peaceful protest, the police automatically identified you, without your consent or knowledge, and stored personal information about you (including photographs of your face) in a secret database?…
Content Type: Call to Action
Support our campaign against unregulated police surveillance technology by sharing our #spypolice posters on social mediaTake part in our #spypolice campaign!
Content Type: Advocacy
India has been leading at developing some of the most complex and intense data-intensive systems in the world as exemplified with their mass biometric identification system, known as Aadhaar, as well as in the development and design of new technologies. To find out more about the main privacy issues in India, check out the State of Privacy in India.
And yet, India does not have a comprehensive privacy legislation and only limited data protection standards can be found under section 43A and…
Content Type: Press release
Below is a joint statement from Privacy International and Bytes for All.
This Friday, 27 September, marks the conclusion of the 24th session of the UN Human Rights Council, a session which has, for the first time, seen issues of internet surveillance in the spotlight. Privacy International and Bytes for All welcome the attention given at the Human Rights Council to this issue. However, we are concerned about developments which took place that threaten privacy rights and freedom of…
Content Type: Press release
The Case
Privacy International v Secretary of State for Foreign and Commonwealth Affairs et al. (Bulk Personal Datasets & Bulk Communications Data challenge)
Date: 5-9 June 2017
Time: from 10:00 onwards
Location: Royal Courts of Justice, The Strand, London WC2A 2LL United Kingdom
Hearing overview
Next week’s hearing follows the Investigatory Powers Tribunal’s earlier judgment in October 2016, which ruled that three issues are to be determined:
…
Content Type: News & Analysis
This post was written by Chair Emeritus of PI’s Board of Trustees, Anna Fielder.
The UK Data Protection Bill is currently making its way through the genteel debates of the House of Lords. We at Privacy International welcome its stated intent to provide a holistic regime for the protection of personal information and to set the “gold standard on data protection”. To make that promise a reality, one of the commitments in this government’s ‘statement of intent’ was to enhance…
Content Type: News & Analysis
This post was written by PI Policy Officer Lucy Purdon.
In 1956, US Presidential hopeful Adlai Stevenson remarked that the hardest part of any political campaign is how to win without proving you are unworthy of winning. Political campaigning has always been a messy affair and now the online space is where elections are truly won and lost. Highly targeted campaign messages and adverts flood online searches and social media feeds. Click, share, repeat; this is what political engagement looks…
Content Type: News & Analysis
20 June 2016
Privacy International joins DRF and A19 in reiterating our serious concerns about the proposed Prevention of Electronic Crimes Bill which is currently being discussed in the Senate in Pakistan. While we note that the Bill adopted by the National Assembly in April 2016 includes some improvements compared to the earlier version, the Bill as currently drafted introduces a series of new provisions that pose a grave risk to freedom of expression and privacy in Pakistan…
Content Type: News & Analysis
7 July 2016
It has been said is that we pay for free services with our personal data. Now, the Privacy Shield exponentially expands this truth and we are paying for the cost of U.S. political dysfunction combined with EU complacency with our privacy. More than four months after the first EU-US Privacy Shield was published on 29 February 2016, a new version has been leaked. Remarkably, it is expected to be adopted.
Four months, two opinions by group of EU data protection…