Don't Celebrate Cellebrite, Because Your Phone Is at Risk

The recent back and forth between Apple and the FBI over security measures in place to prevent unauthorised access to data has highlighted the gulf in understanding of security between technologists and law enforcement. Modern debates around security do not just involve the state and the individual, the private sector plays a very real role too. There are worrying implications for the safety and security of our devices. Today, a new company stepped in to this discussion -- though it had been advertising its ability to break into Apple devices as far back as 2014, according to a brochure acquired by Privacy International.
An Israeli company Cellebrite is reportedly the mysterious party that contacted the FBI about circumventing the safety measures on an iPhone. It is unclear why it has taken so long for this to occur but the proceedings, which Privacy International submitted an intervention to, between Apple and the FBI have been placed temporarily on hold. The revelation that some of Apple’s safety features may be vulnerable to attack will not sit well with their security engineers who strive to keep our information secure and safe. It should also be a cause for concern to all iPhone users given that criminals could use the same techniques against them. Whatever avenue is used to undermine these safety mechanisms, it is vital that they are closed off by Apple as soon as possible.
Cellebrite is a mobile phone forensics company that has attended trade shows in the UK and abroad for many years. The company has been mentioned on the BBC spy show The Fall and even made an appearance in CSI: Cyber. Alongside the company’s appearance in fictional spy shows, Privacy International has retrieved some direct marketing from the company’s brochures when attending secretive trade shows. While much of the advertising previously available shows the company providing capabilities for SIM Card cloning and Android devices, it has also claimed capability for operating on Apple operating systems.
Privacy International has found similar forensics systems previously used in Colombia by the DAS security agency, which were subsequently disbanded for their involvement in human rights abuses, including illegal surveillance. The Israeli authorities are currently proposing to regulate the export of such forensics tools in sweeping export regulations.
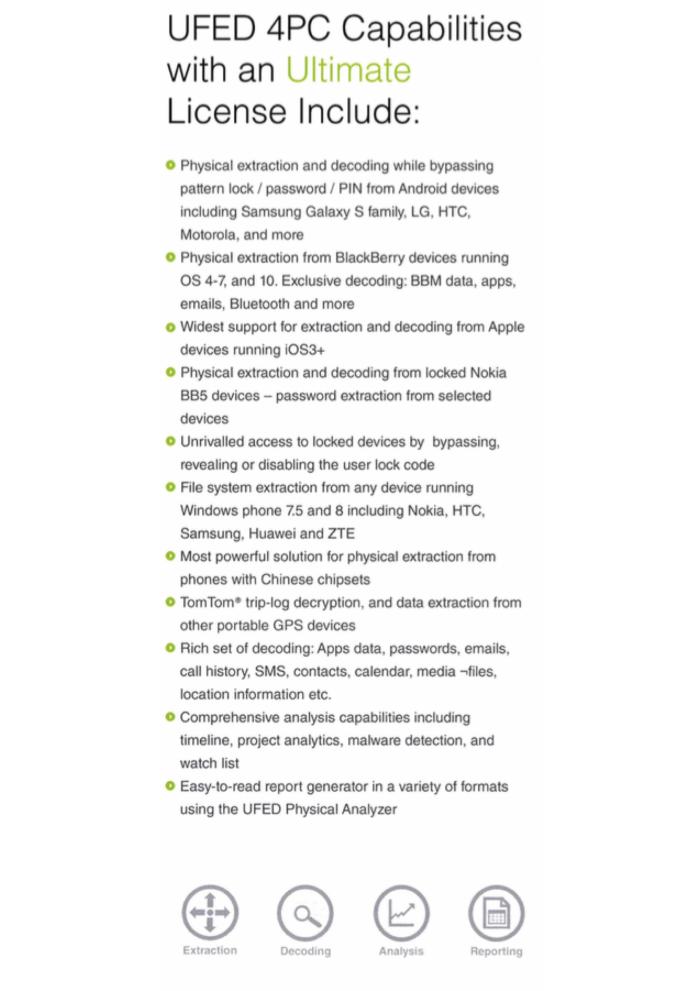
Revealed by Privacy International today, an excerpt from a recently acquired brochure shows Cellebrite advertising the “Widest support for extraction and decoding from Apple devices running iOS3+”. This capability comes at a price, Cellebrite has tiered license platforms. The company’s ‘Ultimate’ option includes many features that would be valuable a government or criminal enterprise, including the extraction of calendars, contacts, and even GPS analysis. Passwords and media files are also part of the extraction suite and a very wide range of hardware is supported by the equipment. The capabilities listed here give the user access to virtually all of the sensitive material contained on the target phone. It is highly unlikely that Cellebrite are the only party with these capabilities.
Apple claims to have devised a number of safeguards to protect against “brute-force” attempts to determine the passcode. First, Apple uses a “large iteration count”, which “functions to slow attempts to unlock an iPhone”. The iteration count is “calibrated so that . . . it would take more than 5 years to try all combinations of a six-character alphanumeric passcode with lowercase letters and numbers.” Second, Apple imposes escalating time delays after each entry of an invalid passcode. Finally, an individual can turn on the “Erase Data” setting, which automatically wipes the keys needed to read the encrypted data after ten consecutive incorrect attempts to enter the passcode. All such protections are in place to keep us and our data safe. In the modern world, penetration testing is one of the most effective ways to find security vulnerabilities. Questions must now be asked about why Apple is not aware of such tools and has not fixed their devices such that they do not betray their users.
The implications are quite serious for customers of US-made technology. The US Government can compel companies to compromise the safety of any or all of these users with a single court order. Furthermore, the U.S. Government considers itself to have the power to compel parties to sign software using private keys. This has massive implications for the trustworthiness of SSL/TLS, which is the protocol that secures traffic to modern websites. However, given the option, it seems the Government would prefer to hack the devices on their own, and in secret. Had Cellebrite come forward before the case was filed, we may never know that iPhones, such as the one in question, are vulnerable to equipment sold by such companies.
This is not a U.S.-only issue. The UK’s proposed Investigatory Powers Bill grants the UK Government the power to compel companies to hack their users, or hack them using their own capabilities and conduct mass surveillance in the form of bulk collection and interception. All of this would be done in secret.