A Hack Job? BT Responds to Report that Claims it Develops Malware for the GCHQ

One of the UK’s largest telecommunications operators, BT, has said to Privacy International that a report claiming it “co-produces malware” with a surveillance company for the GCHQ is inaccurate – but hasn’t said why or given any more details.
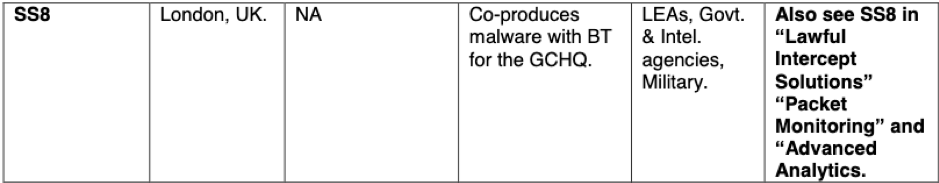
The accusation was made by C5IS – a shadowy online publication claiming to be “the most widely read source of information on surveillance technologies”. In its Big Black Book of Electronic Surveillance, it claims that SS8, a high-profile US surveillance company with offices in the UK, “Co-produces malware with BT for the GCHQ”.
So we put this to BT, asking them:
Is it accurate that BT ‘co-produces malware’ with SS8 for the UK’s primary signals intelligence agency, GCHQ?
- If the above is accurate, could you:
- Elaborate on what BT’s relationship is with SS8;
- Describe what is meant by ‘producing malware’;
- Describe how such malware is used;
- Describe how such production is governed and overseen within BT.
- If the report is not accurate:
- Does BT currently have or has it ever had a commercial relationship with SS8, and if so, what is/was the nature of that relationship?
- Does BT carry out any activity which could be described as ‘producing malware’?
- Will BT contact the publishers of the report to state that the report is not accurate?
Responding, BT have said:
We can confirm that it isn’t accurate.
We do use penetration testing, which may include replicating test versions of malware/malware attacks for the sole purpose of testing the integrity of our networks.
I’m afraid we can’t comment on your other question for legal reasons.
C5IS first appeared some years ago as an online magazine known as Insider Surveillance – purporting to offer expert analysis and commentary on the electronic surveillance industry. It does not provide information on its sources.
So while their accusation may be wrong or at the least misleading, it is still disappointing that BT has refused to directly address the questions or confirm if they will ask for a correction, considering the gravity of the claim.
BT’s statement that the report “isn’t accurate” doesn’t address which specific assertion is inaccurate, while failing to provide any information on its relationship with SS8 or in developing malware doesn’t inspire confidence. If such an important assertion is wholly without foundation, BT should be able to ask for a correction – and we recommend that it does so.
We have again asked BT to address this, and will update this page with any further information.