Search
Content type: Report
First published in 2017, PI’s Guide to International Law and Surveillance is an attempt to collate relevant excerpts from these judgments and reports into a single principled guide that will be regularly updated. This is the fourth edition of the Guide. It has been updated it to reflect the most relevant legal developments until March 2024.The Guide aspires to be a handy reference tool for anyone engaging in campaigning, advocacy, and scholarly research, on these issues. The fourth…
Content type: Advocacy
While PI recognises the threats posed by cybercrime, PI reiterates the need both for a narrow scope for the proposed Convention, focusing solely on core cyber-dependent crimes, as well as for effective safeguards throughout the entire treaty to ensure human rights are respected and protected, especially in the areas of privacy and freedom of expression. Throughout the negotiations most of proposals by Member States and other stakeholders aimed at restricting the scope of the treaty and…
Content type: Video
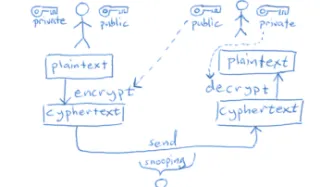
Links - Read more about PI's work on encryption- Matt Blaze and crypto.com; you can now find Matt at mattblaze.org - More about ITAR and the export of cryptography- More about France's ban on encryption ending in this 1999 article from the Register- More about the Data Encryption Standard - Find out more about the Clipper Chip or take a look at this NY Times article from 1994 (paywalled)- Matt Blaze's flaw in the Clipper Chip- NSA Data Center and NSA holding data- An…
Content type: Video
The case dealt with a Russian law obliging telecommunications service providers to indiscriminately retain content and communications data for certain time periods, as well as a 2017 disclosure order by the Russian Federal Security Service requiring Telegram Messenger company to disclose technical information which would facilitate “the decoding of communications”.Links:PI case pageECtHR judgment in the Podchasov casePI's work on encryptionPI's report on End-to-End Encryption (E2EE)More…
Content type: Video
LinksFind out more about encryption:Computerphile on YouTube is a computer science professor with a range of useful and accessible videos on encryptionCloudflare have a helpful learning centre including this article on how encryption works and why cloudflare use Lava lamps to generate keysThis is a helpful article on Diffie-Hellman including a diagram of the colours demonstration, which Ed discusses during the podcastThis article is great for learning more about hashingAnd if you're interested…
Content type: Advocacy
Privacy International had suggested the Human Rights Committee consider the following recommendations for the UK government:Review and reform the IPA 2016 to ensure its compliance with Article 17 of the ICCPR, including by removing the powers of bulk surveillance;Abandon efforts to undermine the limited safeguards of the IPA 2016 through the proposed Investigatory Powers Amendment Bill;Refrain from taking any measures that undermine or limit the availability of encrypted communications or other…
Content type: Advocacy
BackgroundThe Snowden revelations and subsequent litigation have repeatedly identified unlawful state surveillance by UK agencies. In response, the UK Parliament passed the highly controversial Investigatory Powers Act 2016 (IPA), which authorised massive, suspicionless surveillance on a scale never seen before, with insufficient safeguards or independent oversight.Privacy International led legal challenges to this mass surveillance regime both before and after the Act became law. The Act…
Content type: Long Read
In June 2023, the UK government announced its proposal to expand its surveillance powers by, among others, forcing communications operators to undermine encryption or abstain from providing security software updates globally. Building on our response to the government’s plans, this piece explains why what they want to do puts every one of us at risk.
Why your trust (to technologies you use) matters
Surveillance and privacy are complex concepts to grasp – it’s part of the appeal to us at PI.…
Content type: Advocacy
This was submitted by PI and EFF for the sixth session of the Ad Hoc Committee, which is due to consider the text in August 2023.
Our submission covers provisions in the chapters related to procedural measures and law enforcement, as well as international cooperation of the proposed UN Cybercrime treaty (full title: Comprehensive international convention on countering the use of information and communications technologies for criminal purposes). We also provide general comments on Article 54…
Content type: Long Read
On 18th January, it was announced that end-to-end encrypted iCloud services, Advanced Data Protection, would be offered to Apple users globally.
The offer of such level of security globally, while overdue, is a key step to ensuring trust and confidence in today’s world. There are too many threats to our data and our rights. Twelve years ago, we called on Apple to encrypt iCloud storage for users all around the world.
Why this is important
While privacy and security is often portrayed as…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: Advocacy
Despite repeated recommendations by the UN Human Rights Council and the UN General Assembly to review, amend or enact national laws to ensure respect and protection of the right to privacy, national laws are often inadequate and do not regulate, limit or prohibit surveillance powers of government agencies as well as data exploitative practices of companies.
Even when laws are in place, they are seldom enforced. In fact PI notes how it is often only following legal challenges in national or…
Content type: Examples
Zoom said it would deliver end-to-end encryption as one of a number of security enhancements to its service, but it will only be available to enterprise and business customers whose identity they can verify and not on the free service. The company says it wants to be able to work with law enforcement in case people use Zoom for a "bad purpose". None of Zoom's competitors offer end-to-end encryption.
Source: CNBC
Writer: Jordan Novet
Content type: Examples
The controversial Israeli spyware company NSO Group's US arm, Westbridge, has been trying to pitch its phone hacking software to US law enforcement agencies such as the San Diego Police Department, particularly a tool called "Phantom", which the complany claims can overcome encryption, track geolocation, withstand a factory reset, monitor apps and voice and VOIP calls, and collect passwords.
Writer: Joseph Cox
Publication: Vice
Content type: Advocacy
Privacy International responded to the call for submissions of the Working Group on the use of mercenaries as a means of violating human rights and impeding the exercise of the rights of peoples to self-determination on role of private military and security companies in immigration and border management and the impact on the protection of the rights of all migrants.
This submission builds on PI’s research and reporting highlighting examples of the involvement of private companies in…
Content type: Examples
Bluetooth utilizes a device pairing mechanism based on elliptic-curve Diffie-Hellman (ECDH) key exchange to allow encrypted communication between devices. The ECDH key pair consists of a private and a public key, and the public keys are exchanged to produce a shared pairing key. The devices must also agree on the elliptic curve parameters being used. Previous work on the "Invalid Curve Attack" showed that the ECDH parameters are not always validated before being used in computing the resulted…
Content type: Examples
An engineering and computer science professor and his team from The Ohio State University discovered a design flaw in low-powered Bluetooth devices that leaves them susceptible to hacking.
Zhiqiang Lin, associate professor of computer science and engineering at the university, found the commonly used Bluetooth Low Energy devices, such as fitness trackers and smart speakers, are vulnerable when they communicate with their associated apps on the owner’s mobile phone.
"There is a fundamental…
Content type: News & Analysis
Photo by Daniel Jensen on Unsplash
Everyone is talking about Facebook's end-to-end encryption plans and the US, UK and Australian government's response. Feeling lost? Here is what you need to know.
What's Facebook trying to do?
First let's be clear: Facebook has many faults when it comes to privacy. It's also suffered a number of security failures recently. See here for instance.
In response to their successive failures to protect your privacy, Facebook announced in their 'pivot to privacy…
Content type: News & Analysis
Today’s announcement regarding the UK and US agreement signed pursuant to the US CLOUD Act is being touted on both sides of the Atlantic as a major victory for law enforcement and security. But it is a step backward for privacy.
And it’s far more complicated than their press release and letter to industry.
The agreement replaces the prior system, under which law enforcement agencies from around the world, including the UK, had to meet US legal standards in order to get access to content held…
Content type: News & Analysis
Privacy International has joined a global coalition of privacy campaigners, tech companies, and technology experts to respond to proposals by British intelligence chiefs aimed at allowing them access to encrypted messaging apps such as WhatsApp or Signal.
If implemented, the proposals would allow government authorities to force messaging platforms to silently add a law enforcement participant to a group chat or call.
Such a capability poses serious threats to…
Content type: Examples
In February 2019 Google engineers announced that they had created faster, more efficient encryption system that could function on less-expensive Android phones that were too low-powered to implement existing full-device encryption. The scheme, known as Adiantum, uses established and well-vetted encryption tools and principles. Android has required smartphones to support encryption since 2015's version 6, but low-end devices were exempt because of the performance hit. It will now be up to device…
Content type: News & Analysis
We found the above image here.
Background
Email is hard to secure. For years we've been trying to build security on top of email, such as through technologies like Pretty Good Privacy (PGP) and the open source implementation: GnuPG (GPG).
What happened
In the past 48 hours, there have been very scary looking reports recommending people switch off PGP in their email clients.
The TL;DR version of this post is:
PGP is not broken by this attack
You absolutely should not stop…
Content type: News & Analysis
Dear Politicians,
With elections coming up and quite a few cringe-worthy comments that have come from many of you and from all sides of the political spectrum, we figured it was time to have a chat about encryption.
First, let’s say what you shouldn’t do:
call for boycotts of companies because they protect their users’ data even from the companies themselves.
say something like “we’ll develop a Manhattan-level project on this” (which, as we’ll remind you, ended up with the creation of a…
Content type: Advocacy
Privacy International's submission on the right to privacy in Thailand, Human Rights Committee, 119th Session.
In our assessment to the Committee, national legislation governing surveillance is inadequate, unclear as to the powers, scope and capacity of state surveillance activities and thus it falls short of the required human rights standards to safeguard individuals from unlawful interference to the right to privacy.
Content type: News & Analysis
Technologists hoped the “Crypto Wars” of the 1990s – which ended with cryptographers gaining the right to legally develop strong encryption that governments could not break – was behind them once and for all. Encryption is a fundamental part of our modern life, heavily relied on by everything from online banking and online shopping services to the security our energy infrastructure.
However, from comments by the French and German governments about creating a European initiative to circumvent…
Content type: Report
The explosion of telecommunications services has improved the ability for human rights groups to disseminate information worldwide. New telephone, facsimile and computer communications have created opportunities for human rights groups to improve organizing and to promote human rights faster and at a lower cost than ever before. However, these new technologies can be monitored by governments and other groups seeking to monitor the activities of human rights advocates. For this reason, human…