Advanced Search
Content Type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content Type: Long Read
In 2022, Privacy International continued to produce real change by challenging governments and corporations that use data and technology to exploit us. And, we produced substantial impact that directly affects each of us.
Here are a handful of our biggest achievements in 2022.
WE CHALLENGED COMPANIES TO CHANGE THEIR BUSINESS MODELS AND PRACTICES
Regulators in UK, France, Greece, and Italy fined and restricted Clearview AI’s activity
Clearview AI built a massive database of our biometrics, by…
Content Type: People
Josie (she/ her) is a Senior Advocacy Officer at Privacy International (PI). Her work focuses on: resisting authoritarianism, protecting the election cycle, people with disabilities' right to privacy, and the surveillance and externalisation of borders.Prior to PI, she held senior roles at the Bahrain Institute for Rights and Democracy (BIRD) focusing on human rights in the Gulf, namely the death penalty, political prisoners, asylum and corporate accountability, and at a child rights NGO in…
Content Type: Video
Links
The organisation who put us in touch with Claudia is called Media Defence, they are an international human rights organisation which provides legal defence to journalists, citizen journalists and independent media around the world who are under threat for their reporting. Find out more about them and their work.
You can also read more about Claudia, her work, and the cases she's taken forward on Media Defence's website.
Claudia's case against the former Administrative Department of…
Content Type: Advocacy
This joint submission to the European Commission consultation on security-related information sharing was signed by Border Violence Monitoring Network (BVMN), Statewatch, Euromed Rights, European Digital Rights (EDRi), Access Now, Privacy International (PI), Refugee Law Lab (York University), Homo Digitalis and the Platform for International Cooperation on Undocumented Migrants (PICUM). Signatures were subsequently added from European Network Against Racism (ENAR), Dr Derya Özkul and Dr Niovi…
Content Type: Long Read
The final report on the 2022 Kenyan election is the result of a collaboration with the Carter Center as part of a joint pre-election assessment focussing on the use of technology in the run up to and during the Kenyan election which took place 9 August. The final report, published this month, follows our preliminary statement of September 2022.
Below we set out a few key observations in connection with the use of data and technology, as well as some of the key data protection incidents.
Key…
Content Type: Video
In January 2023, the UK's Investigatory Powers Tribunal handed down a landmark judgment. The Tribunal held that there were “very serious failings” at the highest levels of MI5 - the UK's domestic intelligence agency - to comply with privacy safeguards from as early as 2014, and that successive Home Secretaries did not to enquire into or resolve these long-standing rule-breaking despite obvious red flags.
In this episode, we talk to Meg Goulding, a lawyer at the UK-based campaigning…
Content Type: Examples
The Mississippi legislature has introduced a bill that would require public schools and postsecondary institutions to install video surveillance cameras that record audio throughout their campuses, including in classrooms, auditoriums, cafeterias, gyms, hallways, recreational areas, and along each campus's perimeter, and allow parents to vies live feeds of classroom instructions. The bill's sponsor, state representative Stacey Hobgood Wilkes (R-Picayune) says the bill's provisions would help…
Content Type: Examples
A US federal judge has ruled in the case Ogiltree v. Cleveland State University that "room scans", the common requirement in remotely proctored exams to provide a 360-degree scan of the area in which students are taking tests, are an unreasonable search under the Fourth Amendment. Often these areas are personal residences and/or private spaces. The ruling is not binding on other courts, but any student wishing to push back against room scans can cite it.https://www.eff.org/deeplinks/2022/08/…
Content Type: Examples
The UK Information Commissioner's Office has reprimanded North Ayrshire council for installing iPayimpact facial recognition technology in nine schools without obtaining adequate consent. The system was intended to speed cashless lunch payments. The council withdrew the system and deleted the data after the ICO's ruling.
https://techmonitor.ai/policy/privacy-and-data-protection/facial-recognition-technology-school-ico
Writer: Sophia Waterfield
Publication: TechMonitor
Content Type: Examples
In a report, the UK's Digital Futures Commission warns that the explosion of use of education technology brings risks to children's privacy, especially that the data it collects, much of it personally identifiable, will be entered into the heavily commercial global data ecosystem, with uncertain consequences for the future. Although schools have returned to in-person learning, tools such as Google Classroom and Class Dojo have become permanently entrenched even though they have "opaque" privacy…
Content Type: Examples
In an unprecedented interim ruling, a student has provided sufficient facts to uphold a complaint that the Free University discriminated against her when its anti-cheating algorithm failed to log her in via face detection, likely due to the darker colour of her skin. The university has ten weeks to prove that the software did not discriminate.
https://www.mensenrechten.nl/actueel/nieuws/2022/12/09/eerste-keer-vermoeden-van-algoritmische-discriminatie-succesvol-onderbouwd
Writer:…
Content Type: Examples
A report finds that most of the education technology endorsed by 49 governments in the rush to online learning during the covid-19 pandemic puts at risk or directly violates the privacy and rights of children for purposes unrelated to their education. Such platforms track children across the internet, access their contacts lists on social media and phones, and built profiles that can be used for manipulation.
https://www.hrw.org/report/2022/05/25/how-dare-they-peep-my-private-life/childrens-…
Content Type: Examples
The pro-Ukrainian hacker group NLB Team leaked the personal data of more than 17 million children and parents who used Moscow Electronic School, an online learning platform that was built by the Moscow city government in 2016 and was its primary method of delivery online education during the covid-19 pandemic. The city government said the leaked data did not pertain to real users; however, a number of users identified their own data. Even before the leak, the platform was reportedly surveilling…
Content Type: Examples
German data protection authorities have ruled that the use of Microsoft Office 365 in schools is not compliant with GDPR, citing a lack of transparency around how and where Microsoft processes and stores student data as well as the potential for third-party access. German federal and state data protection authorities have been looking at how to improve Office 365 for two years but deems changes Microsoft has made insufficient to bring the software into compliance.
https://www.computerweekly.…
Content Type: Examples
In a report, the Center for Democracy and Technology finds that student privacy laws are insufficient to protect students in the face of increasing use of remote education technologies and insufficient staff and other resources. CDT examined the practices of 43 local education authorities and their relationships with their state education agencies in order to understand what information is transparently and proactively available to families, staff, and other stakeholders.
https://cdt.org/…
Content Type: Examples
In a report, the Privacy Coimmissioner of Canada has said that online proctoring tools used to conduct remote exams fail to get sufficiently free, clear, and individual consent from students. Besides this overreach, the report identifies factors that may trigger false alerts and errors in the biometric tools incorporated into the software. The report ends by calling for reflection on how to identify uses of AI that should be prohibited.https://www.biometricupdate.com/202211/online-proctoring-…
Content Type: Examples
The French minister of national education and youth has advised schools not to use the free versions of Microsoft Office 365 and Google Workspace because French public procurement contracts require payment. Paid versions may be allowed if they do not violate data protection rules, including a 2020 French ruling that cloud services that store data in the US are not compliant with GDPR.
https://www.theregister.com/2022/11/22/france_no_windows_google/
Writer: Thomas Claburn
Publication: The…
Content Type: Examples
In a preliminary ruling, the administrative court of Montreuil suspended the use of algorithmic e-proctoring software called TestWe after students at the Institute of Distant Study of the University of Paris 8 brought a legal case, assisted by La Quadrature du Net. The plaintiffs argued that the software failed to comply with GDPR because the software failed to comply with data minimisation standards and its visual and audio surveillance was disproportionate to the intended purpose. A final…
Content Type: Examples
A security flaw in the mandatory "Diksha" app operated by the Education Ministry, which became an important tool for giving students access to coursework while at home during the pandemic, exposed the data of millions of Indian students and teachers for more than a year when a cloud server hosted on Microsoft Azure was left unprotected. In 2022, Human Rights Watch found that Diksha was able to track students location, and shared data with Google, which indexed more than 100 files from the…
Content Type: Advocacy
The submission provides PI’s information and analysis of some of the topics listed in the call. The widespread use of new technologies presents both opportunities and challenges for the protection of human rights, including the right to life and the right to privacy. PI believes that is essential that states take a human rights-centered approach in their use of these technologies, and ensure that their use is consistent with international human rights law. By doing so, states can ensure that…
Content Type: Advocacy
Privacy International (PI) welcomes the zero draft of the WHO convention, agreement or other international instrument on pandemic prevention, preparedness and response (“WHO CA+”). PI has sought to closely follow and engage with the discussions leading up to the draft treaty, despite the significant limitations to civil society participation in the process.
PI believes that the zero draft offers a good basis for negotiations. In particular, we welcome the inclusion of a provision on…
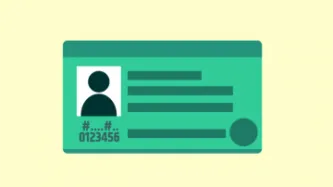
Content Type: Case Study
This piece was written by Privacy International, based on publicly available information and on research by our partners at Hiperderecho
Overview
The Documento Nacional de Identidad (DNI) is the personal ID card recognised by the Peruvian State in any situation where a person might have to identify themselves, be it in an administrative, judicial, civil, or commercial context. The DNI also grants its holder the right to vote.
The DNI issuing and overseeing body is the Registro Nacional de…
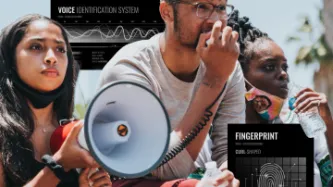
Content Type: Advocacy
Privacy International (PI), the European Center for Not-for-Profit Law (ECNL), International Network of Civil Liberties Organizations (INCLO), Agora, the Canadian Civil Liberties Association, Centro de Estudios Legales y Sociales in Argentina, the Irish Council for Civil Liberties, KontraS in Indonesia, the Legal Resources Center in South Africa, and Liberty in the UK welcome the opportunity to provide input to the global study of the UN Special Rapporteur on the promotion and protection of…
Content Type: News & Analysis
Our mobile phones contain all kinds of data that ranges from photos, videos and emails to information about our health, the places we visit and our leisure time. This data is often relied upon by law enforcement authorities in criminal investigations.
Mobile phone extraction (MPE) tools are used for this purpose as they enable police and other authorities to download content and associated data from people’s phones. These tools are supplied by private companies to security forces and…
Content Type: Long Read
In August 2021, PI published the report An unhealthy diet of targeted ads where we uncovered how personal data was shared by diet companies through their online ads and online testing. Our findings were quite grim, with highly sensitive personal data shared with third parties without consent.
Following this initial report, we performed follow-up research with the same methodology and by September 2021 we reported a number of positive changes from two of these websites: BetterMe and VShred.…
Content Type: Report
PI has been fighting against police using intrusive & disproportionate surveillance technologies at protests around the world for years. Unregulated surveillance and indiscriminate intrusions on our privacy have a chilling effect on the right to freedom of assembly.
We've fought to uncover the types of technologies that police secretly deploy at protests, and we have detailed how protesters around the world can try to protect their intimate and sensitive data from being captured by the…
Content Type: Long Read
We won our case against the UK’s Security Service (MI5) and the Secretary of State for the Home Department (SSHD). The Investigatory Powers Tribunal (IPT) – the judicial body responsible for monitoring UK’s intelligence and security agencies – held that MI5 acted unlawfully by knowingly holding people’s personal data in systems that were in breach of core legal requirements. MI5 unlawfully retained huge amounts of personal data between 2014 and 2019. During that period, and as a result of these…