While there is no internationally accepted definition of cybersecurity, the dominant discourse around the world, promoted by policy-makers and government agencies, focuses on international crime, prevention of terrorism and the quest for ever increased surveillance of our communications and data.
Despite the multitude of warnings evident in the continuing global data breaches from poorly secured databases in companies and governments’ networks, leading actors in this field, both private and public, have not prioritised addressing the root causes of insecure systems and governments have continued to adopt policies and pass laws that undermine cyber security as a whole and therefore place human rights at risk.
What's the problem
We live and share a huge amount of our lives online, depending on our devices and vast global networks to keep us connected. This dependence means there is much at stake and much to protect and secure. Vulnerable or insecure systems can lead to hacks and data breaches that leave people vulnerable and are catastrophic for privacy.
When Governments argue for security they often focus on criminalising and monitoring online behaviour through repressive cyber crime laws and increasing state surveillance powers rather than addressing the root problem of insecure systems.
Companies and governments build systems, devices, networks and services that accumulate vast data stored without proper regard to risk, security, or data minimisation.
All of these approaches ultimately make people and their data less secure, and violate human rights.
With this approach, there is a good chance that essential work will be under-resourced or ignored, such as securing critical infrastructure and supporting security research that identifies vulnerabilities – all of which is an investment in securing systems for the future.
What is the solution?
Human rights should be at the heart of cyber security.
Privacy International believes that protecting and defending individuals, devices and networks should form the basis of any cyber security strategy. They are interlinked and interdependent. Defending security means having to get all this right, simultaneously.
Individual: As more of our lives are lived online, personal data has become increasingly valuable. The value of the data is exactly why companies and governments want to collect, access, and mine it, and criminals want to steal it.Individuals should be empowered to make informed decisions on how to manage their data, how to secure their data and devices, and ultimately how to manage boundaries to counter power imbalances in face of interferences by private and public actors. However, whilst it is important to give individuals back control, it is essential to avoid putting the onus on individuals to protect themselves as this approach plays down the responsibilities of companies, governments and other stakeholders.
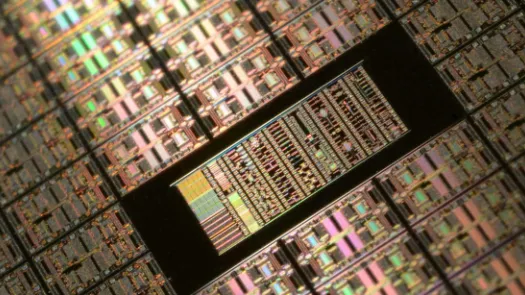
Devices: While it is cheap to connect devices to the internet, it is generally agreed among security experts that the security of devices such as routers, webcams and other household objects connected to the internet known as the “Internet of Things” is very poor. Many devices have poor security such as no or default passwords, and are difficult or even impossible for everyday users to change. Therefore, many of these internet-connected devices are vulnerable, and the proliferation of insecure connected devices in turn are a potential threat to personal and network security. Securing devices should be a key cyber security objective, both for the risk they pose in relation to the personal data they generate, collect and transmit and for the security risks they pose as integrated in or as part of a network.
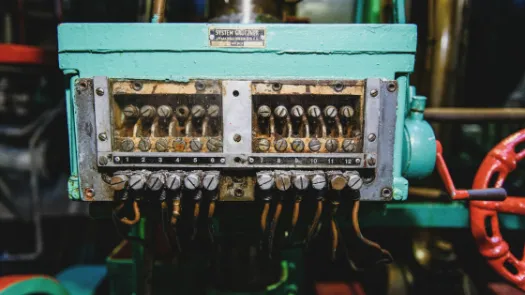
Networks: How to secure networks is an integral yet often neglected part of cyber security policy discussions. Good network security means reducing the attack surface and then allowing the right people through the right devices to access the right services on a network, and keeping everyone and everything else out. Protecting and defending a network can mean protecting a home Wi-Fi connection, a company’s intranet, a telecommunications network accessed by the public, a bank’s network, an industrial control system (ICS) in a factory, or a nation’s critical infrastructure such as a power grid.
What PI is doing
With the rise of new security challenges around malicious hacking, excessive data generation and data processing, and the challenges posed by the ever-increasing number and types of devices connected to the internet, PI is cultivating and developing new narratives around security. We are exploring the relationship of the protection of national infrastructures and personal data security. The cybersecurity discourse has a great potential to liberate us all from the stale debates about security v privacy and through the exploration of the cybersecurity policies in various countries across the world we are looking to explore the mutual benefits of protecting security and privacy.
Working with national and international experts across disciplines, we are undertaking research, advocacy and policy work to enable an environment whereby:
- cybersecurity challenges are framed around the individual and their devices that hold sensitive personal information that need to be secured, thereby removing the current policy emphases that focus on greater surveillance and datasharing powers of government agencies and industry;
- there is transparency of publicprivate partnerships which arise as government institutions outsource their administration and security needs to the private sector, and that such partnerships are subject to rigorous accountability mechanisms;
- cybersecurity laws and policies are designed to respect and protect human rights, rather than curtail them.