What types of data can law enforcement extract from my phone?
A mobile device is a huge repository of sensitive data, which could provide a wealth of information about its owner and many others with whom the user interacts.
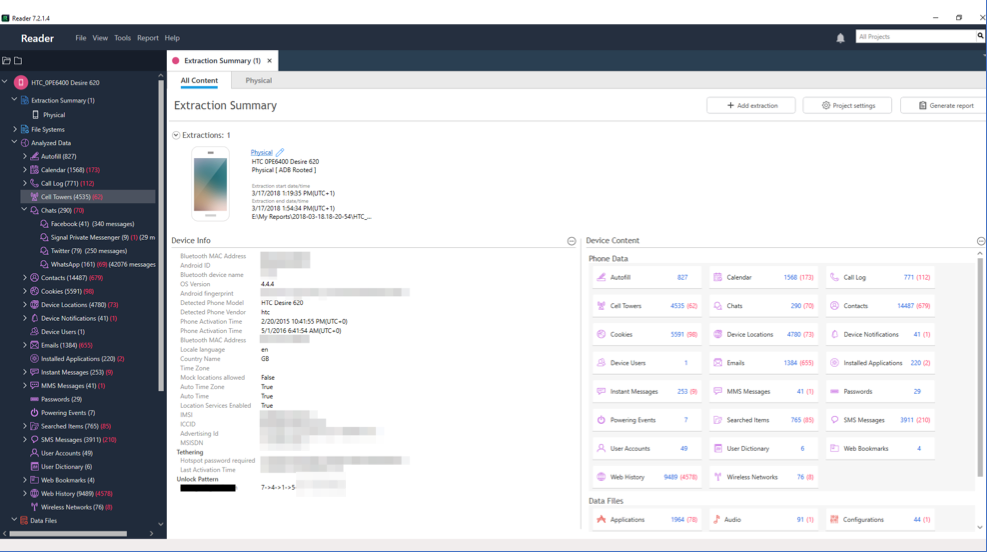
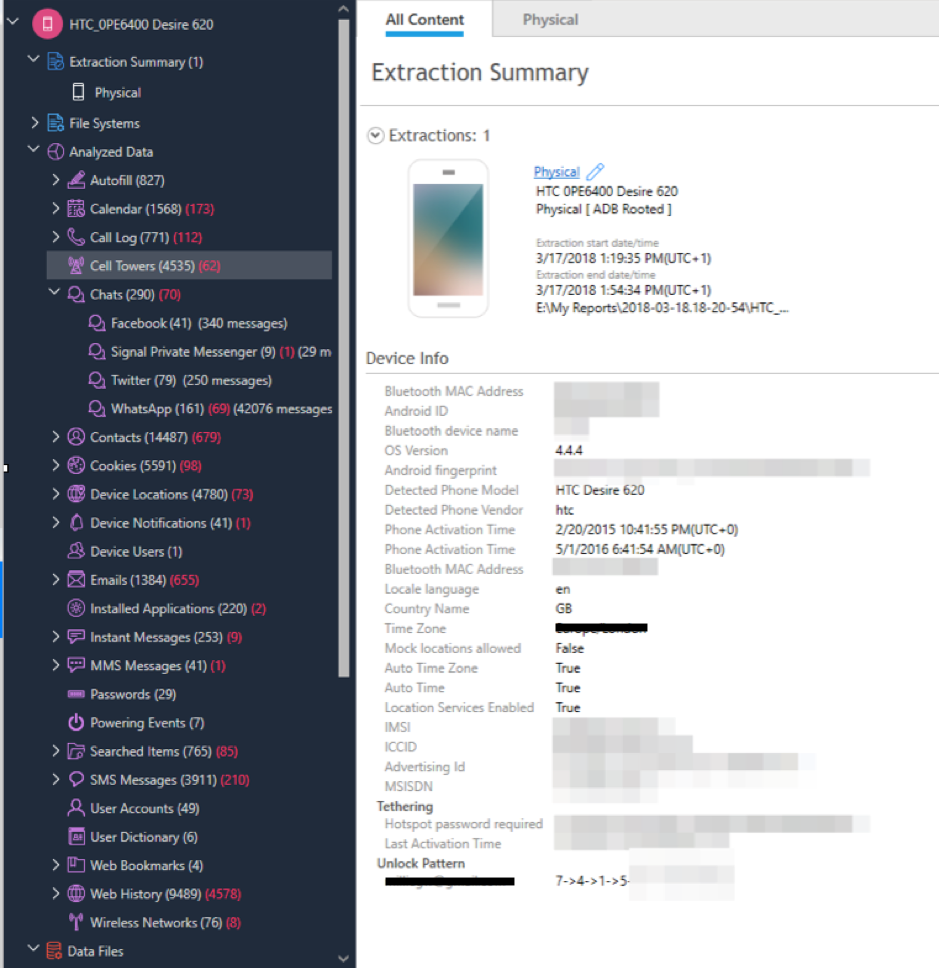
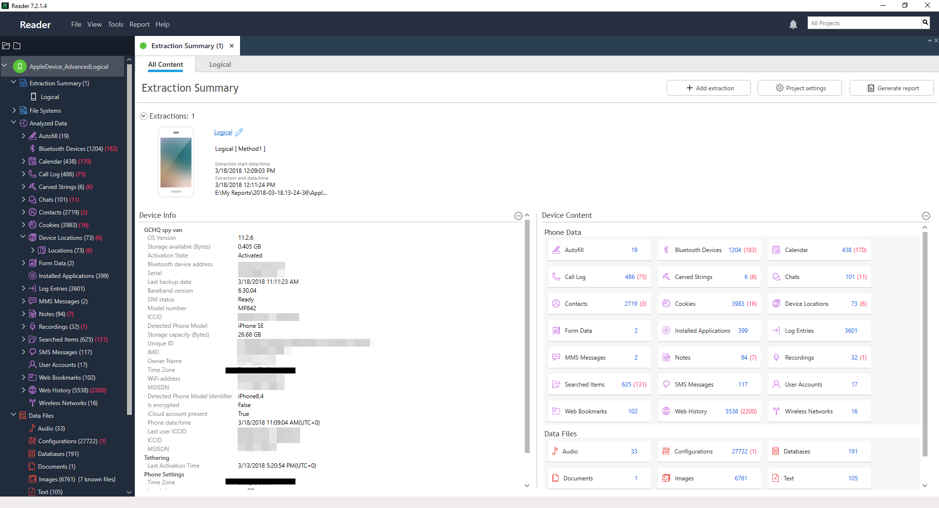
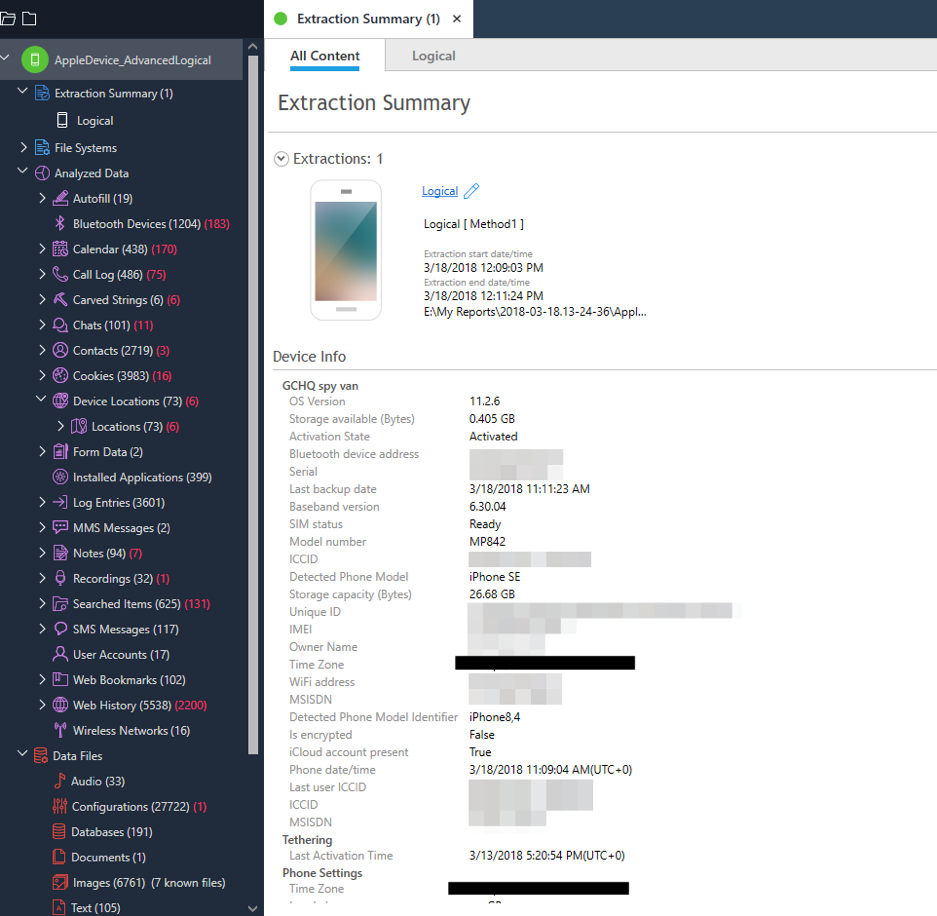
Companies like Cellebrite, MSAB and Oxygen Forensics sell software and hardware to law enforcement. Once your phone is connected to one of these mobile phone extraction tools, the device extracts, analyses and presents the data contained on the phone.
What data these tools can extract and what method is used will depend on the operating system, security features and phone model.
Privacy International used Cellebrite’s UFED to extract an Android phone (HTC Desire) using a Physical [ADB Rooted] extraction. The images below are real examples of what a police officer might be able to see if they can extract data from your phone. The numbers in red are deleted items.
Privacy International also extracted data from an iPhone SE using a logical extraction. Again, the numbers in red are deleted items that were retrieved.
Read more:
Surveillance Company Cellebrite Finds a New Exploit: Spying on Asylum Seekers https://privacyinternational.org/feature/2776/surveillance-company-cellebrite-finds-new-exploit-spying-asylum-seekers


