Advanced Search
Content Type: Long Read
Creative Commons Photo Credit: Source
In the midst of continued widespread public outrage at the US government’s brutal ‘zero-tolerance’ policy around immigration – multiple data and analytics companies have quietly avoided answering questions about their role in feeding the US Immigration and Customs Enforcement (ICE) agency’s data backbone. These companies are bidding to work with an agency that has time and time again shown itself to be a brutal and problematic.
Privacy International…
Content Type: Press release
Privacy International has today released a report that looks at how powerful governments are financing, training and equipping countries — including authoritarian regimes — with surveillance capabilities. The report warns that rather than increasing security, this is entrenching authoritarianism.Countries with powerful security agencies are spending literally billions to equip, finance, and train security and surveillance agencies around the world — including authoritarian regimes. This is…
Content Type: Press release
On the day that GDPR comes into force, PI has launched a campaign investigating a range of data companies that make up a largely hidden data ecosystem. This hidden data ecosystem is comprised of thousands of non-consumer facing data companies - such as Acxiom, Criteo, Quantcast - that amass and exploit large amounts of personal data. Using the rights and obligations provided for within the new data privacy law, PI's campaign involves investigating a selection of these companies whose business…
Content Type: Impact Case Study
PI and our global partners have been at the forefront of challenging communications data retention for over a decade.
What is the problem
Communications data, also known as metadata, tells a story about your digital activity and answers the who, when, what, and how of a specific communication. While communications data doesn't include the contents of a message, all of the other information about the message can be very revealing about people, their habits, thoughts, health and personal…
Content Type: Impact Case Study
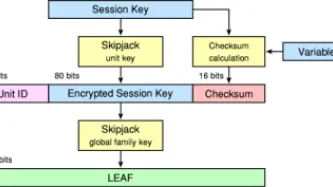
What happenedThe Clinton Administration kicked off the cypto-wars in 1993 with the Clipper Chip. The continued application of export controls restrained the deployment of strong cryptography in products at a key moment of internet history: as it began to be embedded in software and networking. What we didIn the early phases of the crypto-wars we placed pressure on global industry to implement encryption in their products. We ran campaigns and events across the world on the need for strong…
Content Type: Impact Case Study
What is the problem
For over two decades we have been documenting an alarming use and spread of surveillance. It is no longer just the wars on terror or drugs or migration that is driving this trend. The management of health crises and distribution of welfare regularly are among others being used to justify this turn to increasingly invasive forms of surveillance. From country to country we see the same ideas and the same profiteers expanding their reach.
When we first released our report on…
Content Type: Impact Case Study
What is the problem
Business models of lots of companies is based on data exploitation. Big Tech companies such Google, Amazon, Facebook; data brokers; online services; apps and many others collect, use and share huge amounts of data about us, frequently without our explicit consent of knowledge. Using implicit attributes of low-cost devices, their ‘free’ services or apps and other sources, they create unmatched tracking and targeting capabilities which are being used against us.
Why it is…
Content Type: Impact Case Study
What happenedIn the aftermath of 9/11, Governments across the world rushed to legislate to expand surveillance. GovernmentsMoved to limit debate and reduce consultations as they legislated with speed.Created new systems to collect data on all travellers, for the purpose of profiling and risk scoring.Expanded identity schemes, and began demanding biometrics, particularly at borders.Developed financial surveillance mechanisms on an unprecedented scale.What we didFew non-governmental…
Content Type: Impact Case Study
What happenedGovernments continuously seek to expand their communications surveillance powers. In the 1990s it was in the context of applying telephone surveillance laws to the internet. In the 2000s a spate of new laws arrived in response to 9/11. Expansions were then sought to monitor over-the-top services within the framing of Web 2.0. Then in the post-Snowden environment Governments rushed to legislate their previously secret powers.What we didWe supported…
Content Type: Impact Case Study
What is the problem
In the 1990s privacy was often maligned as a ‘rich Westerner’s right’. We were told often that non-Westerners didn’t need privacy and had different cultural attitudes and would greet surveillance policies and technologies — often exported from the West.
Global civil society was composed mostly of a few individuals with no resources but great passion. The larger and more established NGOs, such as consumer and human rights organisations were less interested in ‘digital’ and ‘…
Content Type: Impact Case Study
What happenedSince the late 1980s governments across the world have been trying to build identity registries. By the early 1990s, there were similar policies being pursued by a number of governments across the Pacific region, with similar technologies from the same companies. In the mid-90s ID cards became a ‘modern’ policy, implementing smart cards. By 9/11 biometric IDs became the preferred solution to undefinable problems. Then came vast databases of biometrics to identify people — with…
Content Type: Impact Case Study
[Photo By Ludovic Courtès - Own work, CC BY-SA 3.0] Last update: 14 December 2022What is the problem and why it is importantUntil the early '10s, the right to privacy had been sidelined and largely unaddressed within the UN human rights monitoring mechanisms, despite being upheld as a fundamental human right in the Universal Declaration of Human Rights and the International Covenant on Civil and Political Rights (ICCPR).Beyond the ICCPR General Comment No.16: Article 17 (…
Content Type: Impact Case Study
What happenedStrong and effective data protection law is a necessary safeguard against industry and governments' quest to exploit our data. A once-in-a-generation moment arose to reform the global standard on data protection law when the European Union decided to create a new legal regime. PI had to fight to ensure it wasn't a moment where governments and industry would collude to reduce protections.In January 2012, the European Commission published a proposal to comprehensively reform the…
Content Type: Long Read
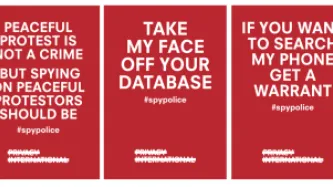
TO TAKE PART IN OUR CAMPAIGN, RIGHT CLICK ON THE PICTURES BELOW, SAVE THEM, AND SHARE THEM ON SOCIAL MEDIA TAGGED #SPYPOLICE
Have you ever been to a peaceful protest, demo or march? Did you assume that the police would only be identifying 'troublemakers'? How would you feel if just by turning up at a peaceful protest, the police automatically identified you, without your consent or knowledge, and stored personal information about you (including photographs of your face) in a secret database?…
Content Type: Call to Action
Support our campaign against unregulated police surveillance technology by sharing our #spypolice posters on social mediaTake part in our #spypolice campaign!
Content Type: Explainer
What is the Global Surveillance Industry?
Today, a global industry consisting of hundreds of companies develops and sells surveillance technology to government agencies around the world. Together, these companies sell a wide range of systems used to identify, track, and monitor individuals and their communications for spying and policing purposes. The advanced powers available to the best equipped spy agencies in the world are being traded around the world. It is a…
Content Type: Report
¿Existen ciudades inteligentes? ¿O son un pretexto para recolectar y procesar más datos? Este informe examina la realidad del mercado de las ciudades inteligentes más allá del uso del término de marketing "inteligente" y las iniciativas existentes. También consideramos las consecuencias y las importantes preocupaciones que surgen en términos de privacidad y otros derechos humanos.
Content Type: Long Read
The battle for Kenyan voters’ allegiance in the 2017 Presidential election was fought on social media and the blogosphere. Paid advertisements for two mysterious, anonymous sites in particular started to dominate Google searches for dozens of election-related terms in the months leading up to the vote. All linked back to either “The Real Raila”, a virulent attack campaign against presidential hopeful Raila Odinga, or Uhuru for Us, a site showcasing President Uhuru Kenyatta’s accomplishments. As…
Content Type: Report
When you rent a car at the airport, use a car-share for a family day trip, one of the first things you are likely to do before setting off on your journey, is to connect your phone to the car. You switch on the Bluetooth and see a list of other people’s phones that were previously connected - Mike’s iPhone, Samsung Galaxy, Bikerboy_Troi, Dee Dee. You input your journey into the navigation, perhaps noticing stored locations of previous drivers.
Seems fairly innocuous? Wrong. Your name and…
Content Type: Report
Financial services are changing, with technology being a key driver. It is affecting the nature of financial services, from credit and lending through to insurance, and even the future of money itself.
The field of fintech is where the attention and investment is flowing. Within it, new sources of data are being used by existing institutions and new entrants. They are using new forms of data analysis.
These changes are significant to this sector and the lives of people it serves. This…
Content Type: Report
The smart city market is booming. National and local governments all over the world expect their cities to become more efficient, more sustainable, cleaner and safer by integrating technology, increasing data generation and centralising data to provide better services. From large multinationals to small start-ups, companies want their slice of the multi-billion dollars per year pie of municipal budgets and long-term government contracts.
But do smart cities even exist? And are our cities…
Content Type: News & Analysis
October 31st 2017 will mark the 3rd World Cities Day (we will forgive if you did not know that), with the general theme “Better City, Better Life.” On this date, PI will be launching its latest report “Smart Cities: Utopian Vision, Dystopian Reality”. This is an opportunity for us to ask: who exactly are our cities going to become better for?
Technology is often given as an answer when we are not sure what the question is. Cities are no exception to that. The current…
Content Type: News & Analysis
Ask people around you if they live in a smart city, and more likely than not they will answer that they don’t. I can tell you that because I have tried.
When giving talks about this very topic in cities like Berlin, The Hague and Stockholm, I always ask this question at the start. The rough ratio I tend to get is that: 15 per cent hesitantly raise their hand to say they do, 60 per cent don’t, 20 per cent just look confused and 5 per cent are not listening.
And yet most people who live in cities…