Search
Content type: Advocacy
Background
In August 2022, Amazon announced that they had entered into a definitive merger agreement to acquire iRobot, a company that specialises in designing and building consumer robots. The transaction was formally notified to the European Commission on 1 June 2023, while the UK Competition and Markets Authority (CMA) has already launched an investigation into the transaction since April 2023.
We believe that this acquisition is likely to significantly impede effective competition in and…
Content type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.
It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content type: Report
Introduction
Several policy initiatives are in progress at the EU level. They seek to address the sustainability of connected devices such as smartphones, tablets and smart speakers. While initiatives to extend the useful life of hardware are important, software must not be ignored. Almost any digital device with which we interact today relies on software to function, which acts as a set of instructions that tells the hardware what to do. From smart thermostats to smart speakers, to our…
Content type: Press release
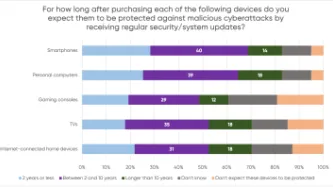
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content type: Advocacy
On 30 March 2022, the European Commission published a proposal for a directive empowering consumers for the green transition, which is is designed to enhancing consumer rights in making informed choices in order to play an active role in the transition to a climate-neutral society. At the moment, the proposal is being discussed by the Committee on the Internal Market and Consumer Protection of the European Parliament.
PI welcomes the aim of the proposal to enhance consumer rights, particularly…
Content type: Examples
Emails obtained by EFF show that the Los Angeles Police Department contacted Amazon Ring owners specifically asking for footage of protests against racist police violence that took place across the US in the summer of 2020. LAPD signed a formal partnership with Ring and its associated "Neighbors" app in May 2019. Requests for Ring footage typically include the name of the detective, a description of the incident under investigation, and a time period. If enough people in a neighbourhood…
Content type: Explainer
With more and more connected devices around us, the chance that you've been hit by an update notification is high. But what do these software updates do? How do they actually work, and why are they important?
Hardware and Software
Modern electronic devices require two main parts to function: the hardware and the software. The hardware usually refers to physical electronic pieces inside a device (usually a collection of microchips, logic gates and specialised processing chips, such as those to…
Content type: Examples
The rush to incorporate greater safety from the coronavirus is bringing with it a new wave of workplace surveillance as companies install tracking software to determine who may have been exposed and which areas need deep cleaning if an employee gets infected; monitor social distancing; and use Bluetooth beacons embedded in badges to locate employees.
Companies are also installing thermal cameras to take employees' temperature as they enter the workplace or public area. Companies are also…
Content type: Examples
Academics have disclosed today a new vulnerability in the Bluetooth wireless protocol, broadly used to interconnect modern devices, such as smartphones, tablets, laptops, and smart IoT devices.
The vulnerability, codenamed BIAS (Bluetooth Impersonation AttackS), impacts the classic version of the Bluetooth protocol, also known as Basic Rate / Enhanced Data Rate, Bluetooth BR/EDR, or just Bluetooth Classic.
The BIAS attack
The BIAS security flaw resides in how devices handle the link key,…
Content type: Examples
Bluetooth utilizes a device pairing mechanism based on elliptic-curve Diffie-Hellman (ECDH) key exchange to allow encrypted communication between devices. The ECDH key pair consists of a private and a public key, and the public keys are exchanged to produce a shared pairing key. The devices must also agree on the elliptic curve parameters being used. Previous work on the "Invalid Curve Attack" showed that the ECDH parameters are not always validated before being used in computing the resulted…
Content type: Examples
An engineering and computer science professor and his team from The Ohio State University discovered a design flaw in low-powered Bluetooth devices that leaves them susceptible to hacking.
Zhiqiang Lin, associate professor of computer science and engineering at the university, found the commonly used Bluetooth Low Energy devices, such as fitness trackers and smart speakers, are vulnerable when they communicate with their associated apps on the owner’s mobile phone.
"There is a fundamental…
Content type: Case Study
In 2015, James Bates was charged with first-degree murder in the death of Victor Collins. Collins was found floating face down in Bates’ hot tub in November 2015. Bentonville police served two search warrants ordering Amazon to turn over the “electronic data in the form of audio recordings, transcribed records, text records and other data contained on the Amazon Echo device” in Bates’ home.
The reason for the warrants? According to the police, just because the device was in the house that…
Content type: Examples
A woman was killed by a spear to the chest at her home in Hallandale Beache, Florida, north of Miami, in July. Witness "Alexa" has been called yet another time to give evidence and solve the mystery. The police is hoping that the smart assistance Amazon Echo, known as Alexa, was accidentally activated and recorded key moments of the murder. “It is believed that evidence of crimes, audio recordings capturing the attack on victim Silvia Crespo that occurred in the main bedroom … may be found on…
Content type: Examples
Denmark released 32 prisoners as part of an ongoing review of 10,700 criminal cases, after serious questions arose regarding the reliability of geolocation data obtained from mobile phone operators. Among the various problems with the software used to convert the phone data into usable evidence, it was found that the system connected the phones to several towers at once, sometimes hundreds of kilometres apart, recorded the origins of text messages incorrectly and got the location of specific…
Content type: Examples
The Lumi by Pampers nappies will track a child's urine (not bowel movements) and comes with an app that helps you "Track just about everything". The activity sensor that is placed on the nappy also tracks a baby's sleep.
Concerns over security and privacy have been raised, given baby monitors can be susceptible to hackers and any app that holds personal information could potentially expose that information.
Experts say the concept could be helpful to some parents but that there…
Content type: Long Read
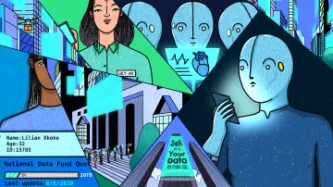
By Valentina Pavel, PI Mozilla-Ford Fellow, 2018-2019
Our digital environment is changing, fast. Nobody knows exactly what it’ll look like in five to ten years’ time, but we know that how we produce and share our data will change where we end up. We have to decide how to protect, enhance, and preserve our rights in a world where technology is everywhere and data is generated by every action. Key battles will be fought over who can access our data and how they may use it. It’s time to take…
Content type: Examples
A 19-year-old medical student was raped and drowned in the River Dresiam in October 2016. The police identified the accused by a hair found at the scene of the crime. The data recorded by the health app on his phone helped identify his location and recorded his activities throughout the day. A portion of his activity was recorded as “climbing stairs”, which authorities were able to correlate with the time he would have dragged his victim down the river embankment, and then climbed…
Content type: Examples
The body of a 57-year-old was found in the laundry room of her home in Valley View, Adelaide, in September 2016. Her daughter-in-law who was in the house at the time of the murder claimed that she was tied up by a group of men who entered the house and managed to escape when they left. However, the data from the victim's smartwatch did not corroborate her story.The prosecution alleged that the watch had recorded data consistent with a person going into shock and losing consciousness. "The…
Content type: Examples
The 90-year old suspect when to his stepdaughter's house at San Jose, California for a brief visit. Five days later, his stepdaugter's body, Karen was discovered by a co-worker in her house with fatal lacerations on her head and neck. The police used the data recorded by the victim's Fitbit fitness tracker to determine the time of the murder. It was been reported that the Fitbit data showed that her heart rate had spiked significantly around 3:20 p.m. on September 8, when her stepfather was…
Content type: Examples
On 14 May 2018, the husband of the victim, a pharmacist living in Linthorpe in Middlesbrough, subdued his wife with insulin injection before straggling her. He then ransacked the house to make it appear as a burglary. The data recorded by the health app on the murder’s phone, showed him racing around the house as he staged the burglary, running up and down the stairs. The victim’s app showed that she remained still after her death apart from a movement of 14 paces when her husband moved her…
Content type: Examples
A man from Middletown, Ohio, was indicted in January 2017 for aggravated arson and insurance fraud for allegedly setting fire to his home in September 2016. Ohio authorities decided and succeeded to obtain a search warrant for the data recorded on the pacemaker after identifying inconsistencies in the suspect’s account of facts. Ohio authorities alleged that the data showed that the accused was awake when he claimed to be sleeping. It has been reported that a cardiologist, examining data from…
Content type: Examples
In yet another murder case, a New Hampshire judge ordered Amazon to turn over two days of Amazon Echo recordings in a double murder case in November 2018.
Prosecutors believe that recordings from an Amazon Echo in the Farmington home where two women were murdered in January 2017 may yield further clues as to who their killer might be. Though the Echo was seized when police secured the crime scene, the recordings are stored on Amazon servers.
Timothy Verrill, of Dover, New Hampshire, was…
Content type: News & Analysis
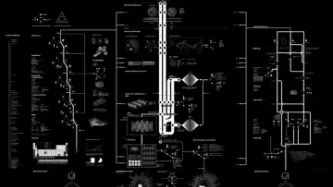
Image: Anatomy of an AI system: a map of the many processes — extracting material resources, data, and human labor — that make an Amazon Echo work. Credit: Kate Crawford and Vladan Joler
With over 6.3 million Amazon Echo devices worldwide, there is a good chance these constantly active devices will record criminal behavior.
Bloomberg, who recently reported on yet another creepy feature, that Amazon workers are listening to what you tell Alexa, were told by workers…
Content type: Long Read
For International Women’s Day 2019, Privacy International looks at some of the key themes around the intersection of gender rights and the right to privacy and we review the work we and our partners have done on those topics.
When dealing with cases of non-consensual sharing of intimate images, often known as ‘revenge porn,’ or doxxing, where a person’s personal details are shared publicly, the link between privacy and online-gender-based violence is very clear. Privacy…
Content type: Examples
Police investigating the 2016 rape and murder of a 19-year-old medical student were unable to search the iPhone of suspect Hussein Khavari, an Afghan refugee who declined to give them his password. The investigators gained access to the phone via a private company in Munich, and went through Apple's health app data to discern what kinds of activities Khavari participated in on the day of the murder. The app identified the bulk of his activity as "climbing stairs". An investigator of similar…
Content type: Examples
In 2015, ABI Research discovered that the power light on the front of Alphabet's Nest Cam was deceptive: even when users had used the associated app to power down the camera and the power light went off, the device continued to monitor its surroundings, noting sound, movement, and other activities. The proof lay in the fact that the device's power drain diminished by an amount consistent with only turning off the LED light. Alphabet explained the reason was that the camera had to be ready to be…
Content type: Examples
In 2015, Chinese authorities banned the 1.6 million members of the country's People's Liberation Army from using smartwatches and other wearable technology in order to prevent security breaches. Army leaders announced the decision after a soldier in the city of Nanjing was reported for trying to use a smartwatch he had been given to take pictures of his comrades because automatic connections could mean the devices uploaded voice and video to the cloud in violation of national security…
Content type: Report
When you rent a car at the airport, use a car-share for a family day trip, one of the first things you are likely to do before setting off on your journey, is to connect your phone to the car. You switch on the Bluetooth and see a list of other people’s phones that were previously connected - Mike’s iPhone, Samsung Galaxy, Bikerboy_Troi, Dee Dee. You input your journey into the navigation, perhaps noticing stored locations of previous drivers.
Seems fairly innocuous? Wrong. Your name and…