Search
Content type: Video
Links Read more about your optionsLearn more about PI's position on the Cyber Resilience Act
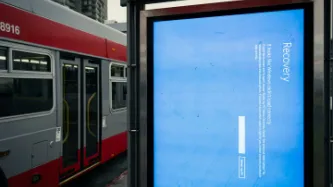
Content type: Long Read
What happened?On 19 July 2024, American cybersecurity company CrowdStrike released an update to its CrowdStrike Falcon software that ultimately caused 8.5 million computers running Microsoft Windows to crash. The damage done was both deep and wide: deep because the computers affected were unable to recover without direct user intervention. Wide because a whole range of companies - from airlines to healthcare to media - across a whole range of countries - from Sweden to India to New Zealand -…
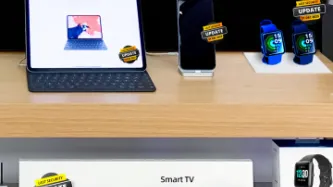
Content type: Report
Introduction
Several policy initiatives are in progress at the EU level. They seek to address the sustainability of connected devices such as smartphones, tablets and smart speakers. While initiatives to extend the useful life of hardware are important, software must not be ignored. Almost any digital device with which we interact today relies on software to function, which acts as a set of instructions that tells the hardware what to do. From smart thermostats to smart speakers, to our…
Content type: Advocacy
Our environment is increasingly populated by devices connected to the Internet, from computers and mobile phones to sound systems and TVs to fridges, kettles, toys, or domestic alarms. There has been research into the negative safety and privacy impacts of inadequate security provided by the software in such devices (such as the creation of large scale botnets). This is also the case with outdated security, a risk enabled by software support periods that are shorter than a product’s usable life…
Content type: Examples
On November 3rd, 2019, [...] a critical vulnerability affecting the Android Bluetooth subsystem [was reported]. This vulnerability has been assigned CVE-2020-0022 and was now patched in the latest security patch from February 2020. The security impact is as follows:
On Android 8.0 to 9.0, a remote attacker within proximity can silently execute arbitrary code with the privileges of the Bluetooth daemon as long as Bluetooth is enabled. No user interaction is required and only the Bluetooth MAC…
Content type: News & Analysis
Privacy International has joined a global coalition of privacy campaigners, tech companies, and technology experts to respond to proposals by British intelligence chiefs aimed at allowing them access to encrypted messaging apps such as WhatsApp or Signal.
If implemented, the proposals would allow government authorities to force messaging platforms to silently add a law enforcement participant to a group chat or call.
Such a capability poses serious threats to…
Content type: Examples
In February 2019 Google engineers announced that they had created faster, more efficient encryption system that could function on less-expensive Android phones that were too low-powered to implement existing full-device encryption. The scheme, known as Adiantum, uses established and well-vetted encryption tools and principles. Android has required smartphones to support encryption since 2015's version 6, but low-end devices were exempt because of the performance hit. It will now be up to device…
Content type: Long Read
Image Source: "Voting Key" by CreditDebitPro is licensed under CC BY 2.0
Democratic society is under threat from a range of players exploiting our data in ways which are often hidden and unaccountable. These actors are manifold: traditional political parties (from the whole political spectrum), organisations or individuals pushing particular political agendas, foreign actors aiming at interfering with national democratic processes, and the industries that provide products that …
Content type: Examples
A 2017 research report found that the most vulnerable smartphone users are the ones whose devices are most open to fraud and harassment. Cheaper, low-end devices are less secure to begin with, and they are also less often replaced than their more expensive counterparts made by. Apple and Google. At any given time there are millions of Android devices that are open to known exploits. Worse, the poorer population that owns these phones are more likely to use them as their sole means of accessing…
Content type: News & Analysis
FREAK, the latest security vulnerability to be exposed that has implications for millions of supposedly secure websites, is just the most recent example of something privacy and security advocates have been saying for some time: when governments meddle with our security technologies, it hurts us all.
When the State advocates for backdoors into our communications, they cannot secure them properly and malicious actors can get in. When our elected officials pontificate about spying on us to…
Content type: News & Analysis
In the wake of tragic attacks in France, politicians from across the world are calling for dramatically expanded surveillance powers, to spy on our phonecalls, ban encrypted communications such as WhatsApp and iMessage, and store details about our international travels for years on end.
If it feels like you've heard this story before, it's because you have. With each violent attempt by extremists to terrorise society, our political leaders dust off old, failed proposals such as the UK…
Content type: News & Analysis
Anonymous proxy service HideMyAss.com - "a leading online privacy website" according to its own homepage - today admitted handing over user logs to law enforcement agencies.
We commend companies running privacy-protecting services. We need more like them. But we also need them to keep their word. Their website claims "Our free web proxy is a secure service that allows you to surf anonymously online in complete privacy" and their pro paid-for version promises that users can "…
Content type: News & Analysis
Other human rights organisations often ask us what they should to when it comes to their infosec needs. Should they run their own mail server, or trust Gmail? Should they merge their calendars by email (!), a local server, or use some cloud solution?
We honestly don't know what to tell them. In fact, we are unsure of what we ourselves should be doing. We know that there are risks of keeping things local (e.g. lack of redundancy), and there are risks of data being stored…