Search
Content type: News & Analysis
Around the world, we see migration authorities use technology to analyse the devices of asylum seekers. The UK via the Policing Bill includes immigration officers amongst those who can exercise powers to extract information from electronic devices. There are two overarching reasons why this is problematic:
The sole provision in the Policing Bill to extract information rests on voluntary provision and agreement, which fails to account for the power imbalance between individual and state. This…
Content type: News & Analysis
It is difficult to imagine a more intrusive invasion of privacy than the search of a personal or home computer ... when connected to the internet, computers serve as portals to an almost infinite amount of information that is shared between different users and is stored almost anywhere in the world.
R v Vu 2013 SCC 60, [2013] 3 SCR 657 at [40] and [41].
The controversial Police Crime Sentencing and Courts Bill includes provision for extracting data from electronic devices.
The Bill…
Content type: Press release
Today the Advocate General (AG) of the Court of Justice of the European Union (CJEU), Campos Sánchez-Bordona, issued his opinion on how he believes the Court should rule on vital questions relating to the conditions under which security and intelligence agencies in the UK, France and Belgium could have access to communications data retained by telecommunications providers.
The AG advises the following:
The UK’s collection of bulk communications data violates EU law.
The French and Belgium…
Content type: Examples
In November 2016 the UK Information Commissioner's Office issued an enforcement notice against London's Metropolitan Police, finding that there had been multiple and serious breaches of data protection law in the organisation's use of the Gangs Violence Matrix, which it had operated since 2012. The ICO documented failures of oversight and coherent guidance, and an absence of basic data protection practices such as encryption and agreements covering data sharing. Individuals whose details are…
Content type: Examples
On 14 May 2018, the husband of the victim, a pharmacist living in Linthorpe in Middlesbrough, subdued his wife with insulin injection before straggling her. He then ransacked the house to make it appear as a burglary. The data recorded by the health app on the murder’s phone, showed him racing around the house as he staged the burglary, running up and down the stairs. The victim’s app showed that she remained still after her death apart from a movement of 14 paces when her husband moved her…
Content type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).
Content type: Long Read
The Privacy International Network is celebrating Data Privacy Week, where we’ll be talking about how trends in surveillance and data exploitation are increasingly affecting our right to privacy. Join the conversation on Twitter using #dataprivacyweek.
In the era of smart cities, the gap between the internet and the so-called physical world is closing. Gone are the days, when the internet was limited to your activities behind a desktop screen, when nobody knew you were a dog.
Today, the…
Content type: Examples
In 2018 a report from the Royal United Services Institute found that UK police were testing automated facial recognition, crime location prediction, and decision-making systems but offering little transparency in evaluating them. An automated facial recognition system trialled by the South Wales Police incorrectly identified 2,279 of 2,470 potential matches. In London, where the Metropolitan Police used facial recognition systems at the Notting Hill Carnival, in 2017 the system was wrong 98% of…
Content type: Long Read
TO TAKE PART IN OUR CAMPAIGN, RIGHT CLICK ON THE PICTURES BELOW, SAVE THEM, AND SHARE THEM ON SOCIAL MEDIA TAGGED #SPYPOLICE
Have you ever been to a peaceful protest, demo or march? Did you assume that the police would only be identifying 'troublemakers'? How would you feel if just by turning up at a peaceful protest, the police automatically identified you, without your consent or knowledge, and stored personal information about you (including photographs of your face) in a secret database?…
Content type: News & Analysis
This op-ed originally appeared in the New Statesman.
Imagine the police searching your home without good reason, without a warrant, without your knowledge. For good measure let’s also imagine that they take a full inventory of all of your possessions and store this in a secret database indefinitely.
A peculiar feature of modernity is that what we would find dystopian in the real world is banal in our virtual world. And the irony is that this can be a greater violation of our privacy and…
Content type: News & Analysis
This op-ed originally appeared in the Huffington Post.
As technologies used by the police race ahead of outdated legislation, we are left vulnerable to potential for misuse and abuse of our data
The vast quantities of data we generate every minute of the day and how it can be exploited is challenging democratic and societal norms. The use by UK police forces of technologies that provide access to data on our phones, which document everything we do, everywhere we go, everyone we interact with…
Content type: Press release
Key points:
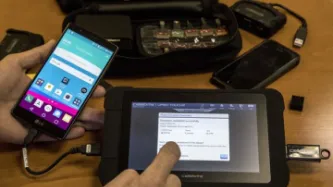
Privacy International have today published a report entitled 'Digital Stop and search: how the UK police can secretly download everything from your mobile phone', based on Freedom of Information requests to 47 police forces across the UK about their use of 'mobile phone extraction' technologies, which enable them to download all the content and data from a mobile phone.
Police forces across the UK are secretly downloading data from the smartphones of people across…
Content type: Report
The ‘Digital stop and search’ report examines the use of ‘mobile phone extraction’ tools by the UK police, enabling them to download all of the content and data from people’s phones.
Privacy International have exposed a potentially unlawful regime operating with UK police forces, who are confused about the legal basis for the technology they are using. The police are acting without clear safeguards for the public, and no independent oversight to identify abuse and misuse of sensitive personal…
Content type: Advocacy
Privacy International has responded to the European Commission’s consultation on the interoperability of EU information systems for borders and security.
The Commission is currently looking at ways in which various border control and policing EU databases and IT systems can be connected to share and exchange more data.
The plans raise a number of concerns as highlighted by Privacy International in our response. These relate to significant potential harms associated with…