Search
Content type: Examples
In the United States, monitoring efforts to combat public benefits fraud are often part of a broader approach that focuses on stigmatizing people receiving benefits and reducing their number, rather than ensuring that the maximum number of people who are eligible receive benefits. However, fraud constitutes less than 1% of the benefits disbursed through the Supplemental Nutrition Assistance Program (SNAP), which are also known as food stamps, and less than 2% of unemployment insurance payments…
Content type: Examples
In the United States, while everyone is surveilled not every is equal when it comes to surveillance. Factors including poverty, race, religion, ethnicity, and immigration status will affect how much you end up being surveilled. This reality has a punitive effect on poor people and their families and places disproportionate burdens on people of minority groups.
https://tcf.org/content/report/disparate-impact-surveillance/?agreed=1
Author: Barton Gellman and Sam Adler-Bell
Publication: The…
Content type: Examples
The vast majority of public benefits programs in the United States—Supplemental Security Income, Temporary Assistance for Needy Families, Medicaid, Children’s Health Insurance Program, Supplemental Nutrition Assistance Programs, the Earned Income Tax Credit, and Housing Assistance—do not take the form of cash transfers. The Temporary Assistance for Needy Families program provides limited cash transfers to families, and it is dependent on families disclosing extensive personal information to…
Content type: Examples
The first conditional cash transfer program in a higher-income country was trialled in the United States by Mayor Bloomberg in New York City from April 2007 to August 2010. Known as Opportunity NYC-Family Rewards, the privately funded pilot program transferred cash rewards to families who were able to meet certain requirements related to children’s education, preventative healthcare, and parents’ employment. Twenty-two different rewards ranged from $20 to $600, and families earned $8,700 on…
Content type: Examples
Virginia Eubanks explains what we can draw from understanding the experience of surveillance of marginalised groups: it is a civil rights issue, technologies carry the bias of those who design them, people are resisting and why we need to move away from the privacy rights discourse.
https://prospect.org/article/want-predict-future-surveillance-ask-poor-communities
Author: Virginia Eubanks
Publication: The American Prospect
Content type: Examples
In this interview with Virginia Eubanks, the author highlights how electronic benefit transfer cards have become tracking devices and how data exploitation used to restrict access to welfare.
https://www.vox.com/2018/2/6/16874782/welfare-big-data-technology-poverty
Author: Sean Illing
Publication: Vox
Content type: Examples
This article is an overview of some of the research documenting how people in vulnerable positions are the ones most affected by government surveillance.
https://stateofopportunity.michiganradio.org/post/technology-opportunity-researcher-says-surveillance-separate-and-unequal
Author: Kimberly Springer
Publication: State of Opportunity Michigan Radio
Content type: Examples
For US citizens who can access benefits, many states use electronic benefit transfer (EBT) cards, which function like debit cards, to distribute benefits. As of 2015, at least 37 states issued Temporary Assistance to Needy Families benefits, also known as welfare, through EBT cards.
http://www.ncsl.org/research/human-services/ebt-electronic-benefit-transfer-card-restrictions-for-public-assistance.aspx
Publication: National Conference of State Legislatures
Content type: Examples
Research from the Brennan Center shows minorities are primarily affected by new laws that restrict citizens access to voting through ID requirement, increased distance to polling station, inconvenient opening hours and hidden costs.
https://www.theguardian.com/world/2012/jul/18/voter-id-poor-black-americans
Writer: Ed Pilkington
Publication: The Guardian
Content type: Examples
The New York Times picked 16 categories (like registered Democrats or people trying to lose weight) and targeted ads at people in them. They used the ads to reveal the invisible information itself, noting that it is a "story of how our information is used not just to target us but to manipulate others for economic and political ends — invisibly, and in ways that are difficult to scrutinize or even question."
The article illustrates that even though data providers don’t…
Content type: News & Analysis
The first half of 2018 saw two major privacy moments: in March, the Facebook/ Cambridge Analytica scandal broke, followed in May by the EU General Data Protection Regulation ("GDPR") taking effect. The Cambridge Analytica scandal, as it has become known, grabbed the attention and outrage of the media, the public, parliamentarians and regulators around the world - demonstrating that yes, people do care about violations of their privacy and abuse of power. This scandal has been one of…
Content type: Advocacy
Consultation Submission
In March 2019, Privacy International submitted a response to a consultation on Disinformation in Electoral Contexts, led by the Office of the Special Rapporteur for Freedom of Expression of the Inter-American Commission on Human Rights together with the Department of Electoral Cooperation and Observation (DECO) and the Department of International Law (DIL) of the Organisation of American States (OAS).
In our submission we highlighted the importance of minmising data…
Content type: Examples
During the November 2018 US midterm elections, Moveon conducted an experiment to test whether it could cheaply and quickly maximise the effectiveness of digital persuasion. The project created a Facebook app called MO Research, and recruited people to answer survey questions about current issues via targeted ads; 400,000 respondents answered an average of five questions each via Facebook Messenger, along with providing information about their hometown, gender, and age that allowed MoveOn to…
Content type: Examples
A December 2018 report prepared by the Oxford Internet Institute's Computational propaganda Research Project and the network analysis firm Graphika for the US Senate Intelligence Committee found that the campaign conducted by Russia's Internet Research Agency during the 2016 US presidential election used every major social media platform to deliver messages in words, images, and videos to help elect Donald Trump - and stepped up efforts to support him once he assumed office. The report relied…
Content type: Examples
Facebook's latest tool for inspecting political ads showed that in the run-up to the US mid-term elections in November 2018, many of the same politicians who had been questioning Facebook about privacy and leaked user data were spending campaign funds on advertisements on the service. Between 2014 and 2018, the digital percentage of political spending rose from 1% to 22% (or about $1.9 billion); between May and November 2018 political spending on Facebook and its subsidiaries came to nearly $…
Content type: Examples
A 2018 study found that Twitter bots played a disproportionate role in spreading the false claim, made by US President Donald Trump shortly after winning the election but losing the popular vote in November 2016, that 3 million illegal immigrants had voted for Democratic opponent Hillary Clinton. After examining 14 million messages shared on Twitter between May 2016 and May 2017, Indiana University researchers found that just 6% of Twitter accounts identified as bots spread 31% of "low-…
Content type: News & Analysis
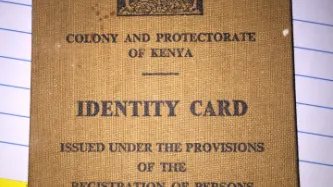
Today, the Kenyan Government is starting their biometric registration exercise known as NIIMS, leading to the issuing of Huduma Namba ID numbers. Along with our colleagues and partners in the human rights community in Kenya, we are very worried about the ramifications of this system for people in Kenya, and particularly for marginalised communities.
Thanks to the hard work and timely action of civil society in Kenya, the judiciary has intervened at the last minute. A court ruling on…
Content type: Long Read
During the last World Economic Forum in Davos, the CEO of Microsoft joined the chorus of voices calling for new global privacy rules, saying the following in regard to the new European General Data Protection Regulation (GDPR):
“My own point of view is that it's a fantastic start in treating privacy as a human right. I hope that in the United States we do something similar, and that the world converges on a common standard."
We have come a long way. From tech companies fighting and…
Content type: Long Read
The Privacy International Network is celebrating Data Privacy Week, where we’ll be talking about how trends in surveillance and data exploitation are increasingly affecting our right to privacy. Join the conversation on Twitter using #dataprivacyweek.
It is often communities who are already the most marginalised who are at risk because of the privacy invasions of data-intensive systems. Across the globe, we see the dangers of identity systems; the harms of online violence against women and the…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgement
The State of Privacy in Kenya is the result of an ongoing collaboration by Privacy International and the National Coalition of Human Rights Defenders - Kenya.
Key Privacy Facts
1. Constitutional privacy protections: Article 31 of the Kenyan Constitution specifically protects the right to privacy.
2. Data…
Content type: News & Analysis
Federal law enforcement is deploying powerful computer hacking tools to conduct domestic criminal and immigration investigations.
By Alex Betschen, Student Attorney, Civil Liberties & Transparency Clinic, University at Buffalo School of Law
Hacking by the government raises grave privacy concerns, creating surveillance possibilities that were previously the stuff of science fiction. It also poses a security risk, because hacking takes advantage of unpatched vulnerabilities in our…
Content type: Press release
FOR IMMEDIATE RELEASE
December 21, 2018
CONTACTS:
Alex Betschen, Civil Liberties & Transparency Clinic, [email protected], 716–531–6649
Colton Kells, Civil Liberties & Transparency Clinic, [email protected], 585–766–5119
Abdullah Hasan, ACLU, [email protected], 646–905–8879
NEW YORK — Privacy International, the American Civil Liberties Union, and the Civil Liberties & Transparency Clinic of the University at Buffalo School of Law filed a lawsuit today…
Content type: News & Analysis
Photo credit: US Immigration and Customs Enforcement
The trial of Mexican drug lord Joaquin “El Chapo” Guzman started in New York back in November 2018. But last week, the jurors were presented with a trove of new key evidence: dozens of text messages exchanged between Guzman, his wife, and his mistresses.
The reason behind this set of revelations? Guzman had been spying on his wife and mistresses, using publicly-available surveillance software called FlexiSpy. Once installed on his targets…
Content type: Examples
In July 2018, Robert Mueller, the special prosecutor appointed to look into Russian interference in the 2016 US presidential election, charged 12 Russian intelligence officers with hacking Hillary Clinton's campaign and the Democratic National Committee by spearphishing staffers. The charges include conspiracy to commit an offence against the US, aggravated identity theft, conspiracy to launder money, and conspiracy to access computers without authorisation. The hack led to the release of…
Content type: Examples
Facebook ads purchased in May 2016 by the Internet Research Agency, a notorious Russian troll farm, urged users to install the FaceMusic app. When installed, this Chrome extension gained wide access to the users' Facebook accounts and web browsing behaviour; in some cases it messaged all the user's Facebook Friends. The most successful of these ads specifically targeted American girls aged 14 to 17 and said the app would let them play their favourite music on Facebook for free and share it…
Content type: Examples
With only days to go before the 2018 US midterm elections, a federal judge ruled that the state of Georgia must change its "exact match" law that required voter registrations with even the tiniest variation from other official identifications to be flagged as potential non-citizens unless they could produce proof of identity. A group of civil rights groups sued Republican secretary of state Brian Kemp, in charge of the elections despite also running for governor, to change the procedure, which…
Content type: Examples
In August 2018, the US Democratic National Committee notified the FBI that the San Francisco-based security company Lookout and the cloud service provider DigitalOcean had detected an attempted hack targeted at the DNC voter database. The attack took the form of a fake DNC login page intended to trick people into disclosing their usernames and passwords thinking they were accessing the DNC's VoteBuilder platrform. Lookout believes it found the site within 30 minutes of its going up online, but…
Content type: Examples
Shortly before the 2018 US midterm elections, Georgia secretary of state and gubernatorial candidate Brian Kemp accused Georgia's Democratic Party of hacking into the state's voter registration database, though without providing any evidence to support the claim. The motives behind the claim were unclear, but a report published by WhoWhatWhy suggested that the claim may have referred to a cybersecurity investigation conducted by the Democrats that uncovered significant flaws in the state's…
Content type: Examples
In July 2018, Election Systems and Software (ES&S), long the top US manufacturer of voter machines, admitted in a letter to Senator Ron Wyden (D-OR) that it had installed pcAnywhere remote access software and modems on a number of the election management systems it had sold between 2000 and 2006. The admission was in direct contradiction to the company's response for a New York Times article earlier in the year on US voting machines' vulnerability to hacking. ES&S says it stopped…
Content type: Examples
In the run-up to the November 2018 US midterm elections, Vice tested Facebook's new system of mandatory "Paid for" disclosure intended to bring greater transparency to the sources of ads relating to "issues of national importance". Placing political ads requires a valid ID and proof of residence. Vice found that Facebook quickly approved ads the site attempted to place that named Islamic State, US vice president Mike Pence, and Democratic National Committee chair Tom Perez in the "Paid for"…