Advanced Search
Content Type: State of Privacy
Introduction
Acknowledgment
The State of Surveillance in Thailand is the result of a collaboration by Privacy International and Thai Netizen Network.
Right to Privacy
The constitution
Thailand experienced a coup d'etat in May 2014. According to Mishari Muqbil and Arthit Suriyawongkul, “their [the junta's] modus operandi seems to be the direct command of ministries and semi-governmental organisations to carry out tasks irrespective of existing legislation.”
Following…
Content Type: Long Read
This briefing highlights opportunities for NGOs to raise issues related to the right to privacy before some selected UN human rights bodies that have the mandate and the capacity to monitor and provide recommendations and redress.
The briefing provides some examples based on Privacy International’s experience and points at additional resources and guides. While this guide focuses on the work of NGOs, information to UN human rights mechanisms can be sent by other civil society actors…
Content Type: Long Read
In this special briefing for International Women’s Day 2017, we explore through the work of the Privacy International Network some areas of concern being addressed in relation to privacy, surveillance, women’s rights, and gender. Coding Rights demonstrates the important of generating and disseminating gendered content on issues of surveillance in Latin America as a means of inciting informed action. In Chile, Derechos Digitales explored the booming market of mobile applications related to…
Content Type: Long Read
Introduction
A growing number of governments around the world are embracing hacking to facilitate their surveillance activities. Yet hacking presents unique and grave threats to our privacy and security. It is far more intrusive than any other surveillance technique, capable of accessing information sufficient to build a detailed profile of a person, as well as altering or deleting that information. At the same time, hacking not only undermines the security of targeted systems, but also has…
Content Type: Long Read
This piece was orignally published in Slate in February 2017
In 2015, the FBI obtained a warrant to hack the devices of every visitor to a child pornography website. On the basis of this single warrant, the FBI ultimately hacked more than 8,700 computers, resulting in a wave of federal prosecutions. The vast majority of these devices—over 83 percent—were located outside the United States, in more than 100 different countries. Now, we are in the midst of the first cases…
Content Type: Report
This investigation looks at how surveillance is being conducted in Thailand. The first part of the investigation focuses on the ties between telecommunication companies and the state, and the second part of the investigation focuses on attacks conducted in order to attempt to circumvent encryption.
Content Type: Long Read
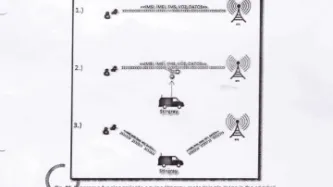
The use of IMSI catchers[1] to arrest individuals is rarely documented — as IMSI catchers are used secretively in most countries. The arrest of Colombian drug lord Henry López Londoño in Argentina is therefore a rare opportunity to understand both how IMSI catchers are used, and also the complexity of their extraterritorial use.
In October 2012, Londoño — also known as Mi Sangre (“My Blood”) — was arrested in Argentina. His arrest was the result of cooperation between the Dirección de…
Content Type: Long Read
The move to digital payments, without an adequate legal framework, is a double-blow to privacy. India is proving to be the case study of how not to do the move to the cashless society. We are seeing in India the deeper drives to digital: linking financial transactions to identity. On the 8th November, Prime Minister Modi of India announced that 500 and 1,000 rupee notes – 86% of the money supply – would be removed from circulation. The initial justification for this was to tackle the…
Content Type: Long Read
In July 2015, representatives of a private company met in a parking lot in Pretoria, South Africa to sell phone tapping technology to an interested private buyer. What they did not know was that this buyer was a police officer. The police had been tipped off that the company was looking to offload the surveillance technology, an IMSI catcher, to anyone who would buy it. It is illegal to operate such surveillance technology as a private citizen in South Africa, and illegal to buy…
Content Type: Report
Privacy International’s investigation contains evidence of the Syrian government’s ambitious plans and projects to monitor the national communications infrastructure, the technical details of which are revealed for the first time. Hundreds of original documents also highlight surveillance trade in this region leading up to and during the Arab Spring, which involved companies from around the world.
Content Type: Long Read
Tech firms and governments are keen to use algorithms and AI, everywhere. We urgently need to understand what algorithms, intelligence, and machine learning actually are so that we can disentangle the optimism from the hype. It will also ensure that we come up with meaningful responses and ultimately protections and safeguards.
Many technologists emerge from University, College or graduate courses with the impression that technology is neutral and believe that all systems they apply their…
Content Type: Long Read
This piece was written by Ashley Gorski, who is an attorney at the American Civil Liberties Union, and PI legal officer Scarlet Kim and originally appeared in The Guardian here.
In recent weeks, the Hollywood film about Edward Snowden and the movement to pardon the NSA whistleblower have renewed worldwide attention on the scope and substance of government surveillance programs. In the United States, however, the debate has often been a narrow one, focused on the…
Content Type: Long Read
On 17 October 2016, the Investigatory Powers Tribunal handed down judgment in a case brought by Privacy International against the Foreign Secretary, the Home Secretary and the three Security and Intelligence Agencies (MI5, MI6 and GCHQ).
The case concerned the Agencies’ acquisition and use of bulk personal datasets (‘BPD’) – datasets that contain personal data about individuals, the majority of whom are unlikely to be of intelligence interest, such as passport databases and finance-related…
Content Type: Long Read
This week, Privacy International, together with nine other international human rights NGOs, filed submissions with the European Court of Human Rights. Our case challenges the UK government’s bulk interception of internet traffic transiting fiber optic cables landing in the UK and its access to information similarly intercepted in bulk by the US government, which were revealed by the Snowden disclosures. To accompany our filing, we have produced two infographics to illustrate the…
Content Type: Long Read
This report examines the emergence of social media based surveillance in Thailand, carried out potentially by people’s own networks of friends and family. It looks at the severe impact this has on personal privacy and points to potential solutions.
In May 2014, Thailand experienced a military coup – its second in eight years. A military government led by General Prayut Chan-o-cha seized power and overthrew the administration of Prime Minister Yingluck Shinawatra. The Army declared martial…
Content Type: Long Read
Often when asked to discuss open data and privacy the objective is to successfully navigate the tension between the fundamental right to privacy, and the virtues of open data. And there is a tension. It is rare to see increased collection of data alongside greater privacy protections. The recently released Surveillance Industry Index (SII) is one of those rarities.
The SII, a joint initiative between Privacy International and Transparency Toolkit, is the largest…
Content Type: Report
The report “The Global Surveillance Industry" charts the development of the industry since the earliest reports in the 70s that wiretapping equipment was being exported by Western countries and used by authoritarian regimes. It provides an accessible introduction into the types of the technologies currently on offer, and uses a combination of export data, company data and analysis of surveillance technologies to assess the current industry. The report presents an analysis of the…
Content Type: Long Read
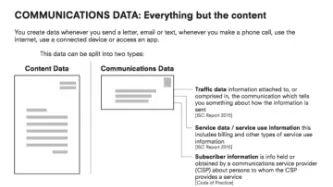
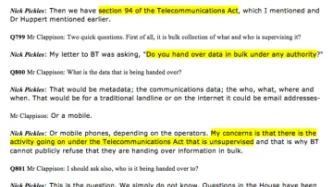
Privacy International’s case on Bulk Personal Datasets and Bulk Communications Data comes to a head with a four-day hearing in the Investigatory Powers Tribunal which commenced on 26 July 2016.
The litigation has brought to light significant revelations about the use of section 94 of the 1984 Telecommunications Act to obtain bulk communications data.
Large amounts of disclosure have shed new light on this hitherto secret power and explained confusing aspects of the Government’s Response to…
Content Type: Long Read
This piece originally appeared here.
On both sides of the Atlantic, we are witnessing the dramatic expansion of government hacking powers. In the United States, a proposed amendment to Rule 41 of the Federal Rules of Criminal Procedure would permit the government to obtain a warrant, in certain circumstances, to hack unspecified numbers of electronic devices anywhere in the world. Meanwhile, across the pond, the British Parliament is currently debating the Investigatory…
Content Type: Long Read
1984: A broad law, a broad power and a whole lot of secrecy
In the wake of litigation brought by Privacy International (‘PI’) and as the Government prepared to introduce the Draft Investigatory Powers Bill (‘IP Bill’) in November 2015, there was a cascade of ‘avowals’- admissions that the intelligence agencies carry out some highly intrusive surveillance operations under powers contained in outdated and confusing legislation.
It is disappointing that it has been almost six months since…
Content Type: Long Read
Written by: Maria del Pilar Saenz
With a raft of recent scandals involving proven and possible abuses of surveillance systems by state institutions, there is a clear need to generate policy and practice in Colombia that promotes respect for human rights. It is necessary to keep this in mind as an emerging public policy discussion on cybersecurity led by CONPES (The National Council for Economic and Social Policy) begins in Colombia. This series of reforms will serve as the policy basis…
Content Type: Long Read
This guest piece was written by Jessamine Pacis of the Foundation for Media Alternatives. It does not necessarily reflect the views or position of Privacy International.
Introduction
With a history immersed in years of colonialism and tainted by martial law, Philippine society is no stranger to surveillance. Even now, tales of past regimes tracking their citizens’ every move find their way into people’s everyday conversations. This, for the most part, has kept Filipinos…
Content Type: Long Read
Written by: Centre for Internet and Society
This guest piece was written by representatives of the Centre for Internet and Society (CIS). It does not necessarily reflect the views or position of Privacy International.
Introduction
As part of the State of the Surveillance project, CIS conducted a review of surveillance law, policy, projects, and trends in India. Below we provide a snap shot of key legal provisions governing surveillance in India and touch on…
Content Type: Long Read
“This is my personal opinion,” concedes Branko, a taxi driver in Skopje, the Republic of Macedonia's capital. “It was done by America to stop Putin building his gas pipe line through Macedonia.”
“This is just politics,” he advises, skeptically.
It's a common reaction to the wiretapping scandal in Macedonia. Beginning in February last year when opposition leader Zoran Zaev posted a series of wiretaps online that he called 'bombs' – they seemingly showed that for years the phone calls of some…
Content Type: Long Read
The recent back and forth between Apple and the FBI over security measures in place to prevent unauthorised access to data has highlighted the gulf in understanding of security between technologists and law enforcement. Modern debates around security do not just involve the state and the individual, the private sector plays a very real role too. There are worrying implications for the safety and security of our devices. Today, a new company stepped in to this discussion -- though it had been…
Content Type: Report
Privacy International notes New Zealand’s written replies to the list of issues prior to reporting in relation to the New Zealand’s laws, policies and practices related to interception of personal communications.
A review of the security and intelligence legislation is currently underway in accordance with the Intelligence and Security Committee Act. It is expected that the Parliament will consider the review in 2016. Hence this represents a significant opportunity to amend the current…
Content Type: Report
The right to privacy is a qualified right. Gender is not and cannot be its qualification.
For this year’s International Women’s Day, the Privacy International Network is sharing some of its successes as well as the challenges and opportunities we face in at the intersection of gender issues and the right to privacy. Click here to see this feature.
Interferences and violations of the right to privacy, as described in the UN Declaration of Human Rights, affect society as a whole. However,…
Content Type: Long Read
Today, Privacy International is publishing the result of a global effort to benchmark surveillance policies and practices in the countries that are part of the Privacy International Network. We’re calling it the ‘State of Surveillance’.We designed a survey of questions based on some key issues: statistics about the communications infrastructure of the country; what civil society organisations and groups that analyse privacy issues; the international and domestic legal framework regulating…
Content Type: Report
Privacy International's new investigation (available in English and in Arabic), 'THE PRESIDENT'S MEN? Inside the Technical Research Department', sheds light on the Technical Research Department, a secret unit of the Egyptian intelligence infrastructure that has purchased surveillance equipment from German/Finnish manufacturer of monitoring centres for telecommunication surveillance, Nokia Siemens Networks, and Italian malware manufacturer, Hacking Team.
Content Type: Long Read
It was summer 2014 when we first came across the acronym TRD while sifting through documents from the company Nokia Siemens Networks (Nokia) that had been leaked to Privacy International. The acronym was explained in the documents: it stood for Technical Research Department.
What we learned from the leak is the TRD had been purchasing an interception management system, a monitoring centre and an X25 network, a legacy technology allowing dial-up internet access. The first two technologies gave…